
In this lab, you will learn to attack SOAP-based web services. More specifically, you would enumerate the WSDL file to discover and invoke hidden methods, bypass SOAP body restriction and perform SQL and Command injection attacks on the provided web service.
\nIn this lab environment, the user will get access to a Kali GUI instance. A slightly modified instance of the Mutillidae web application can be accessed using the tools installed on Kali at http://demo.ine.local.
\nObjective: Perform the following attacks on the provided SOAP-based web service and collect all three flags (flag1, flag2, and flag3):
\n- WSDL Enumeration\n- Invoking hidden methods\n- Bypass SOAP body restrictions\n- SQL Injection\n- Command Injection
Flag Information:\n- flag1 and flag2 would be retrieved by invoking the hidden methods.
\n- flag3 would be invoked from the server file system after exploiting the command injection vulnerability.

The web services to be attacked can be located here:\n- WSDL Enumeration, Invoking hidden methods, SQLi, bypassing SOAP body restrictions: http://demo.ine.local/webservices/soap/ws-user-account.php\n- Command Injection: http://demo.ine.local/webservices/soap/ws-lookup-dns-record.php
\nThe best tools for this lab are:
\nPlease go ahead ONLY if you have COMPLETED the lab or you are stuck! Checking the solutions before actually trying the concepts and techniques you studied in the course will dramatically reduce the benefits of a hands-on lab!
", "tasks": "", "tasks_html": "", "published_date": "2020-10-20T15:32:26Z", "solutions": "# Solution\n\n**Step 1:** Open the lab link to access the Kali GUI instance. \n\n\n\n**Step 2:** Check if the provided machine/domain is reachable. \n\n**Command:**\n```\nping -c3 demo.ine.local\n```\n\n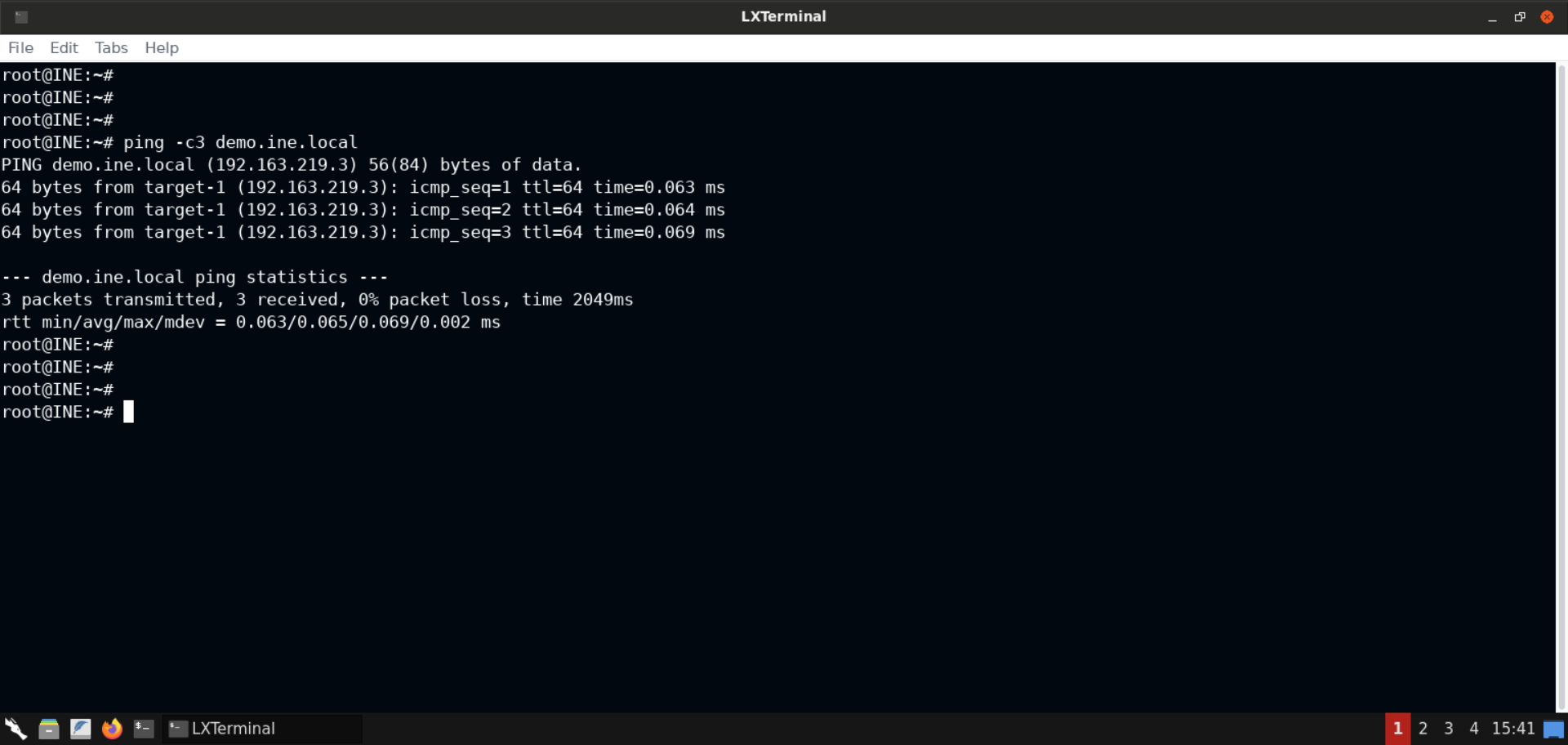\n\nThe provided machine is reachable. \n\n**Step 3:** Check open ports on the provided machine.\n\n**Command:**\n```\nnmap -sS -sV demo.ine.local\n```\n\n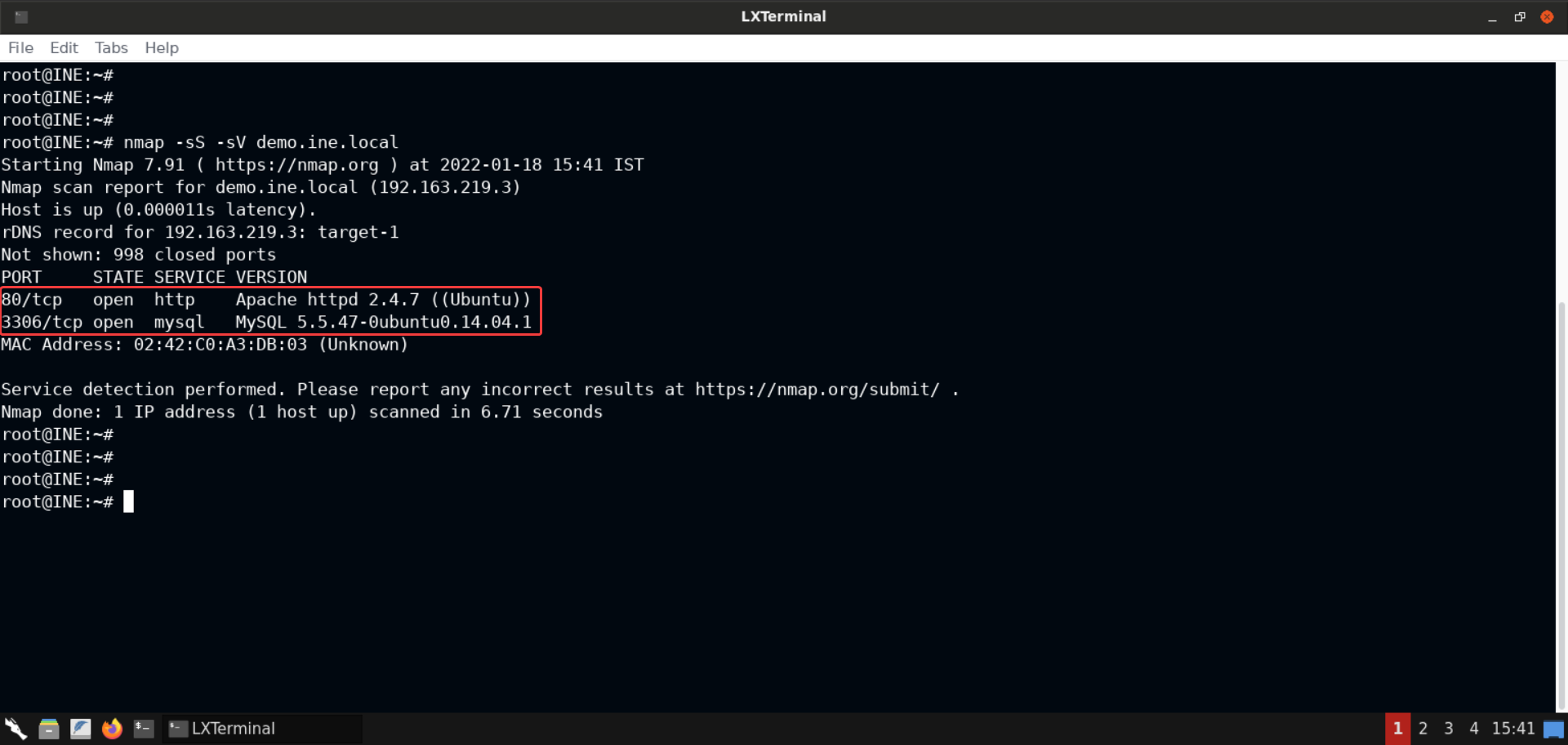\n\nPort 80 (Apache webserver) and 3306 (MySQL server) are open on the target machine. \n\n**Step 4:** Open the browser to inspect the hosted website. \n\n**URL:** http://demo.ine.local\n\n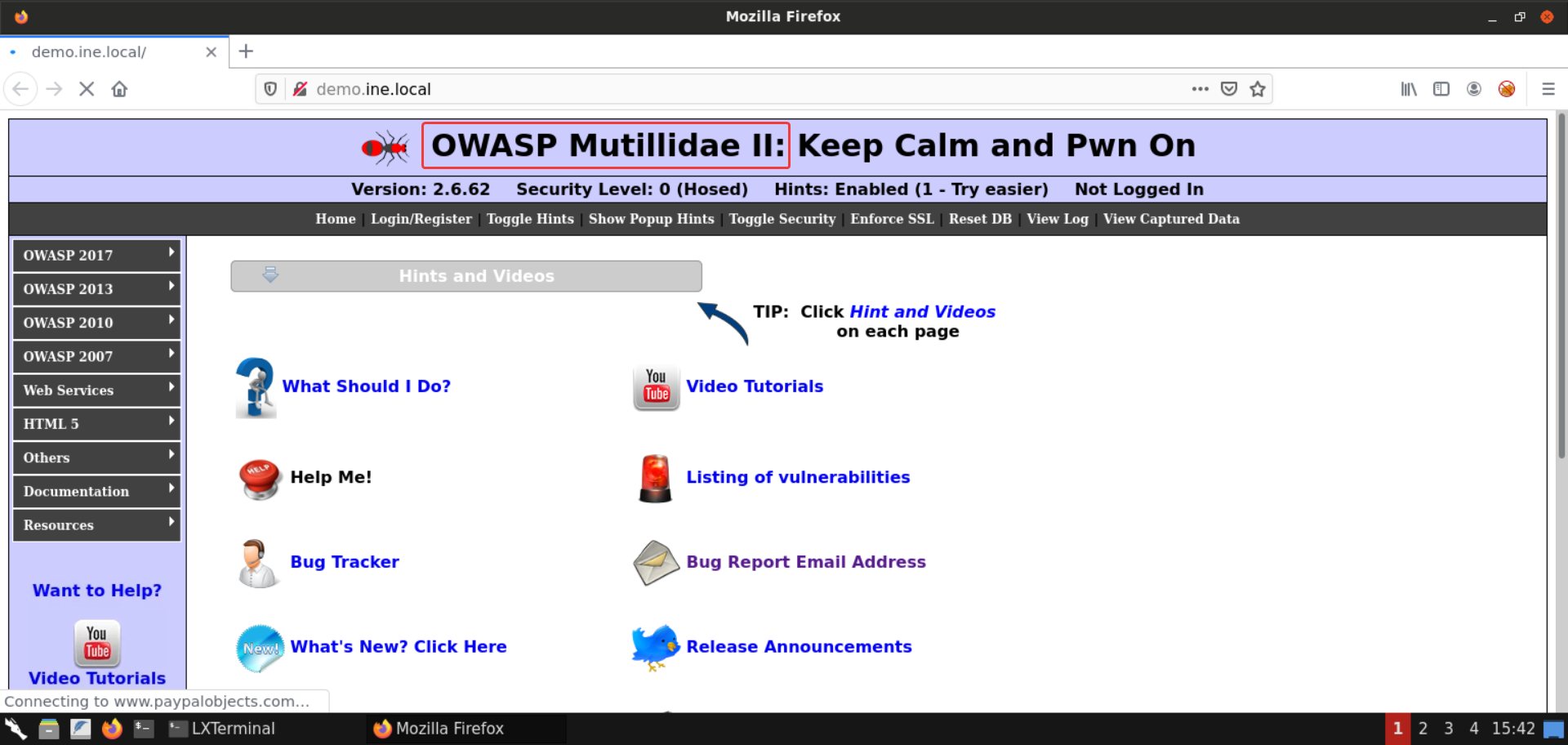\n\nAn instance of [**OWASP Mutillidae II**](https://github.com/webpwnized/mutillidae) is hosted on the Apache webserver. \n\n**Step 5:** Open the **Lookup User** web service. \n\nIn the challenge description, the link for the web services is already provided. \n\nYou could navigate to the web services from the menus available on the web page: \n\nVisit **Web Services** > **SOAP** > **Username Enumeration** > **Lookup User**: \n\n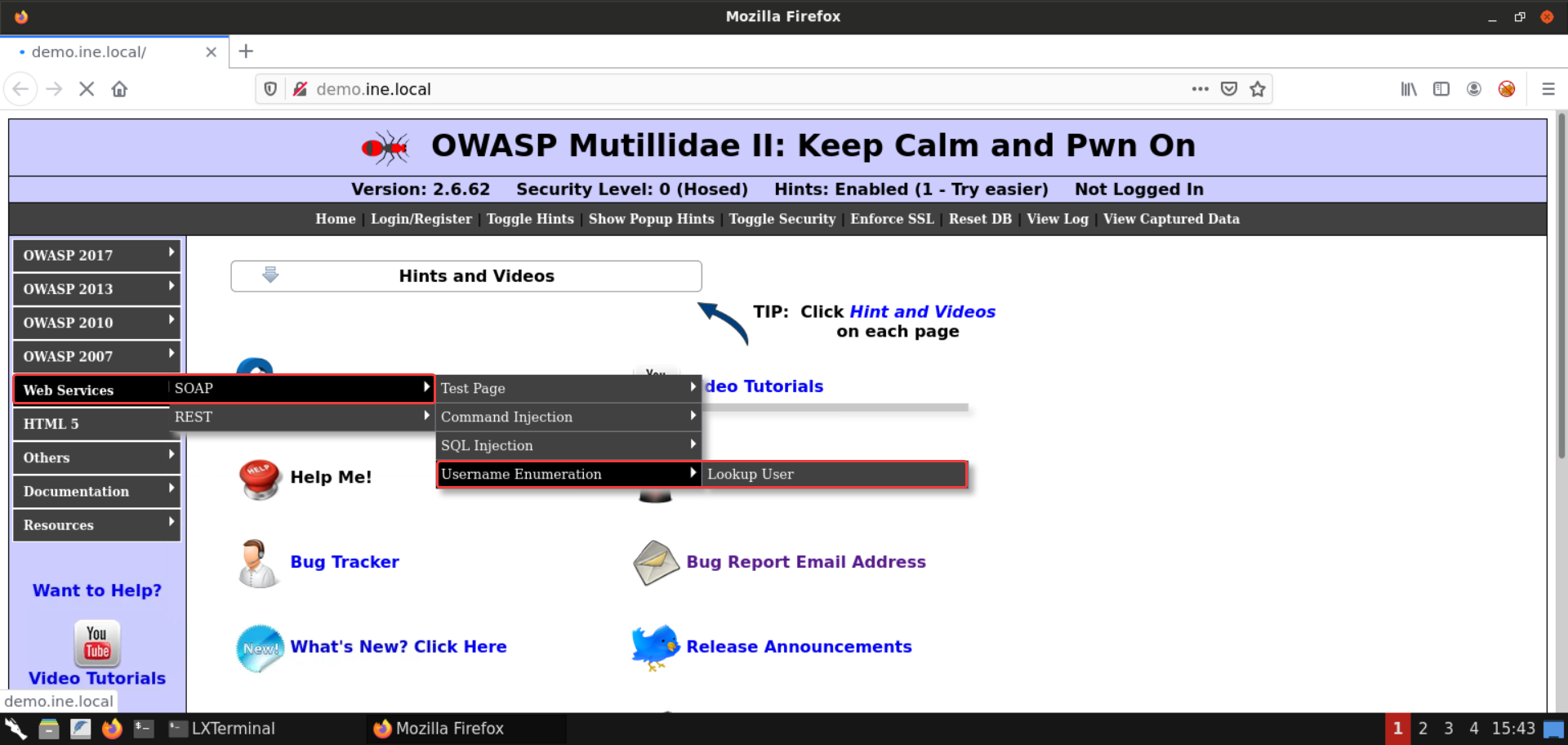\n\nAlternatively you can visit the web service URL provided in the challenge description: \n\n**URL:** http://demo.ine.local/webservices/soap/ws-user-account.php\n\nAnd that should take you to the following web page: \n\n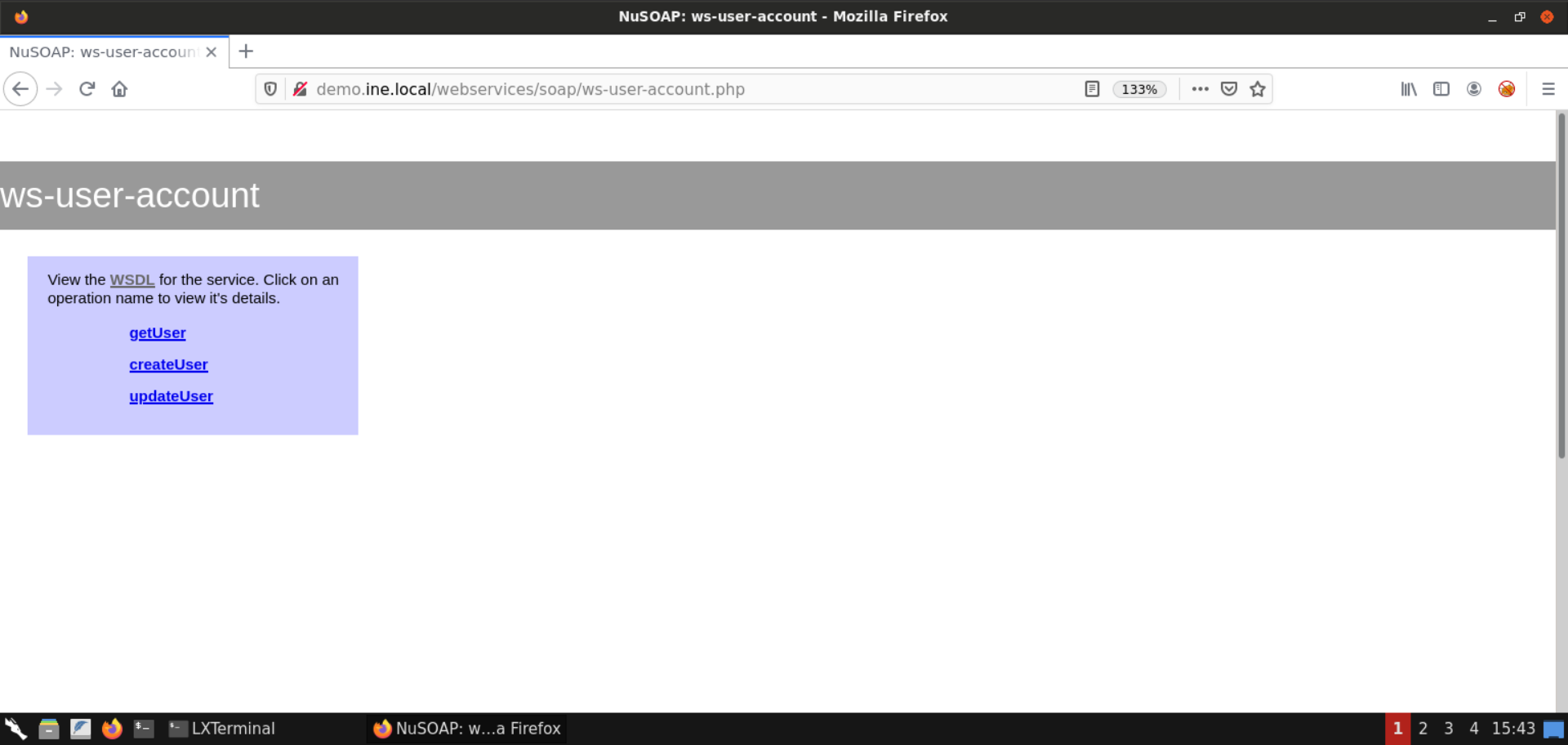\n\n**Step 6:** Enumerate the WSDL file. \n\n**Information:** \nWSDL stands for Web Services Description Language and is used to describe web services. It is written in XML. \n\nA WSDL document describes a web service. It specifies the location of the service, and the methods of the service, using these major elements:\n\n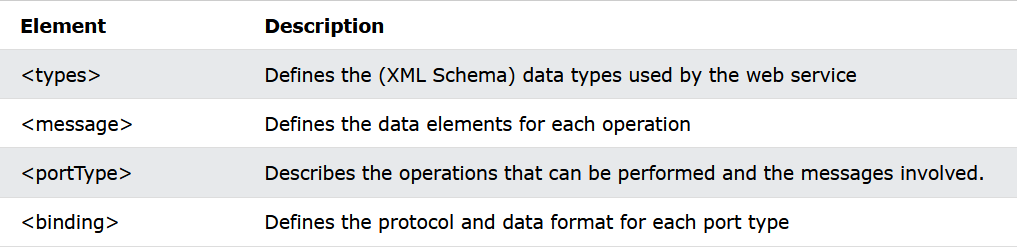\n\n**Reference:** https://www.w3schools.com/xml/xml_wsdl.asp\n\nAnd that's why this file is quite interesting since it's a description of the web service we will be pentesting. \n\nWe would be locating all the defined operations/methods of the service and the parameters they accept to invoke those later. \n\nOn the web service page, click on the **WSDL** file link or append `?wsdl` to the URL: \n\n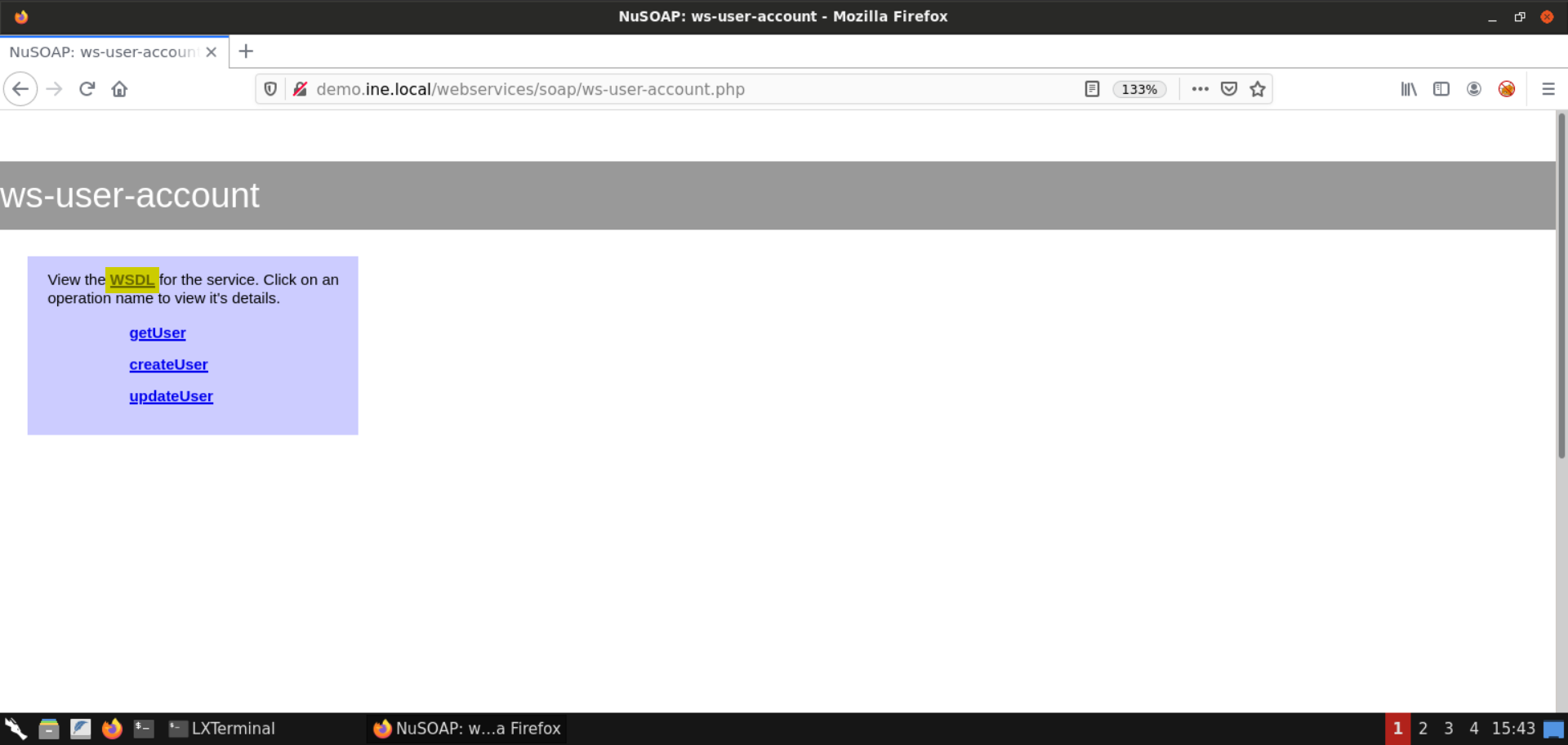\n\nThat would show the WSDL file for the web service we will be interacting with: \n\n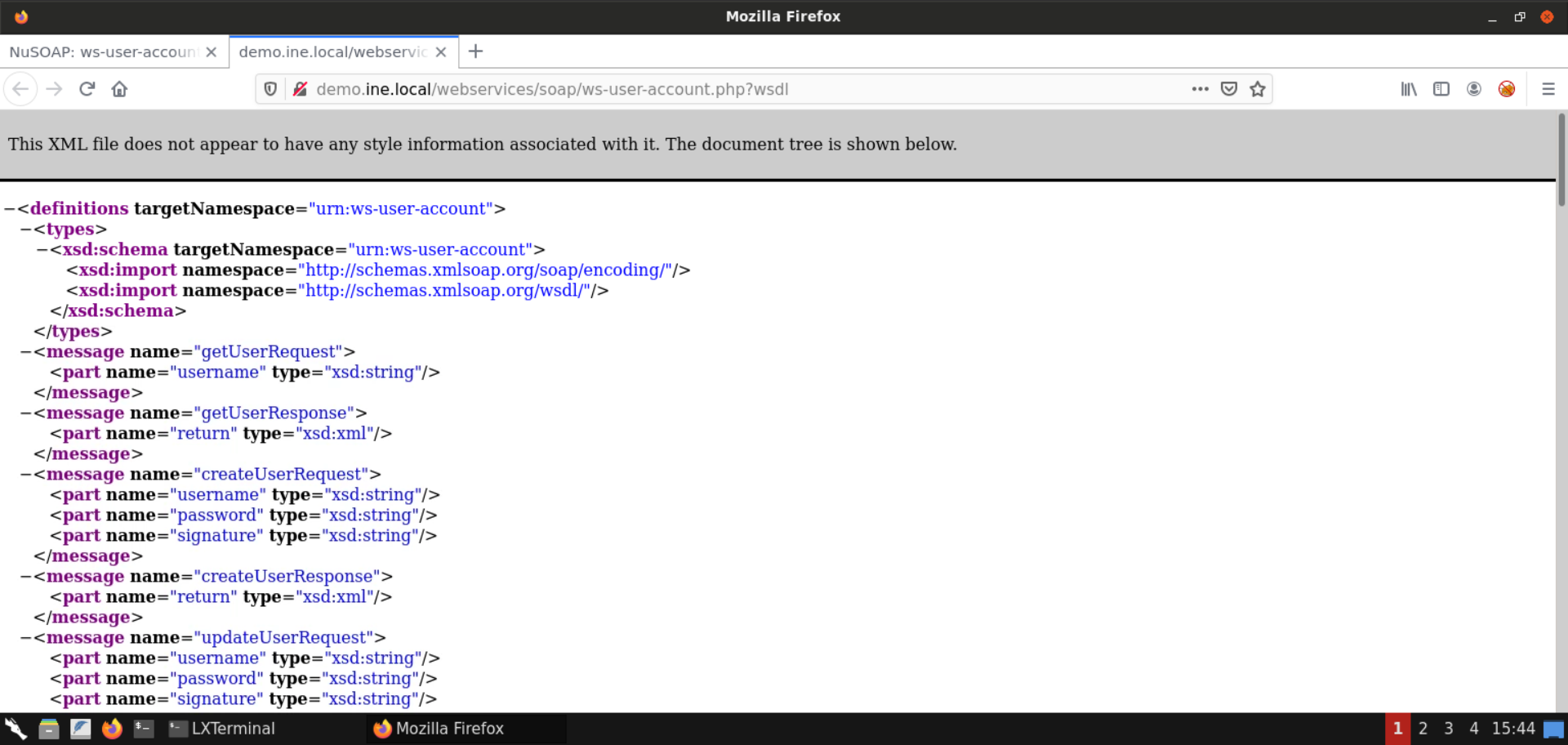\n\nAs we already saw on the [W3schools WSDL page](https://www.w3schools.com/xml/xml_wsdl.asp), `Step 1: Open the lab link to access the Kali GUI instance.
\n
Step 2: Check if the provided machine/domain is reachable.
\nCommand:\n
ping -c3 demo.ine.local
The provided machine is reachable.
\nStep 3: Check open ports on the provided machine.
\nCommand:\n
nmap -sS -sV demo.ine.local
Port 80 (Apache webserver) and 3306 (MySQL server) are open on the target machine.
\nStep 4: Open the browser to inspect the hosted website.
\nURL: http://demo.ine.local
\n
An instance of OWASP Mutillidae II is hosted on the Apache webserver.
\nStep 5: Open the Lookup User web service.
\nIn the challenge description, the link for the web services is already provided.
\nYou could navigate to the web services from the menus available on the web page:
\nVisit Web Services > SOAP > Username Enumeration > Lookup User:
\n
Alternatively you can visit the web service URL provided in the challenge description:
\nURL: http://demo.ine.local/webservices/soap/ws-user-account.php
\nAnd that should take you to the following web page:
\n
Step 6: Enumerate the WSDL file.
\nInformation:
\nWSDL stands for Web Services Description Language and is used to describe web services. It is written in XML.
A WSDL document describes a web service. It specifies the location of the service, and the methods of the service, using these major elements:
\n
Reference: https://www.w3schools.com/xml/xml_wsdl.asp
\nAnd that's why this file is quite interesting since it's a description of the web service we will be pentesting.
\nWe would be locating all the defined operations/methods of the service and the parameters they accept to invoke those later.
\nOn the web service page, click on the WSDL file link or append ?wsdl to the URL:

That would show the WSDL file for the web service we will be interacting with:
\n
As we already saw on the W3schools WSDL page, <portType> describes the operations that can be performed by the web service along with the messages (or the parameters) that have to be passed.
If you check the WSDL for the web service, you will find that it supports five operations, namely:
\n \n
\n
The documentation for all of these operations is also available in the WSDL file.
\nThe conclusion is that the web service page only lists 3 out of these 5 operations. So seemingly, these operations are not meant to be invoked by the normal users and are probably reserved for the administrators.
\nStep 7: Check information on getUser operation.
Head back to the web service page and click on the getUser link:

As you can see, the information on the getUser operation is listed. The input, and output parameters are also listed here. All this information is also present in the WSDL file which we explored in the last step.
Scroll down to view the complete request to invoke the getUser method of the web service:

Step 8: Launch Burp Suite.
\nOpen the start menu and select: 03 - Web Application Analysis -> burpsuite
\n
If you get a warning about the JDK version, feel free to ignore it and press the OK button:
\n
Create a temporary project:
\n
We will be using the default Burp Suite configuration:
\n
After these steps, Burp would start up!
\n
Step 8: Invoke the getUser method.
Open the Repeater window in Burp Suite:
\n
Copy the request to invoke the getUser method from the web page and paste it in the Repeater window:

Remove the /mutillidae part of the URL as the web service is located at /webservice and not at /mutillidae/webservice.
Once that is done, send the request.
\nThat should open a dialog asking for the Host and the Port of the target machine:
Host: demo.ine.local\nPort: 80
\n
Now with the target configured, click on the send button again:
\n
Now the request worked!
\nScroll down the response and you would notice the username and signature returned by the web service:

Step 10: Invoke the deleteUser method.
Replace all the occurences of getUser with deleteUser and end the request:

As you can see in the above image, we got back a 200 response!
\nScrolling down reveals about an error:
\n
As you can see in the above image, there's a parameter that is missing from the request sent to the web service.
\nBut more importantly, we were able to invoke the web service that was supposedly hidden.
\nHead over to the web service's WSDL file and locate deleteUserRequest:

As you can notice in the above image, there are two parameters accepted by this function, namely: username and password. Both of them are of the string data type.
Step 11: Performing SQL Injection attack.
\nNow we know that the deleteUser requires two parameters. But we don't know the password of any of the users.
We could perform a dictionary attack. Alternatively, we could check if the web service is vulnerable to SQL Injection.
\nLet's go with the latter. First, we will send a single quote (') as the password and see if any errors are returned from the web service:

As you can see, we again get back a 200 response.
\nScrolling down reveals a SQL error:
\n
The SQL query executed by the web service is also revealed in the error message:
\nSQL Query:\n
SELECT username FROM accounts WHERE username='Jeremy' AND password=''';As you can see, there is a single extra quote (') which invalidated the whole SQL query.
So we are sure that an SQL Injection vulnerability is present in the web service!
\nNow we will send the following SQL injection payload:
\n' or '1'='1The above payload would result in the following SQL query being executed by the web service:
\nSQL Query:\n
SELECT username FROM accounts WHERE username='Jeremy' AND password='' or '1'='1';The condition on the right side of the OR clause would always evaluate to true since '1'='1' and therefore, even when the conditions on the left side evaluate to false, the result would still be true!
Therefore, sending the above payload in the password field should delete the account for the user named Jeremy:

Scrolling down reveals the account deletion message:
\n
As you can see, we also get back the first flag:
\nflag1: 6701f2d8bf691da5ee694d3a1786a7e6
\nStep 12: Invoke the getAdminInfo method.
Check the WSDL file for the parameters required to invoke the getAdminInfo method:

As you can see in the above image, no parameters are required to invoke the getAdminInfo method.
Scroll down to the view the documentation for the getAdminInfo method:

This method retrieves some (non-sensitive) account details for the admin user. A sample request has also been provided.
\nHead over to Burp Repeater and send the following request:
\nRequest:\n
POST /webservices/soap/ws-user-account.php HTTP/1.1\nAccept-Encoding: gzip,deflate\nContent-Type: text/xml;charset=UTF-8\nContent-Length: 387\nHost: localhost\nConnection: Keep-Alive\nUser-Agent: Apache-HttpClient/4.1.1 (java 1.5)\n<soapenv:Envelope xmlns:xsi=\"http://www.w3.org/2001/XMLSchema-instance\" xmlns:xsd=\"http://www.w3.org/2001/XMLSchema\" xmlns:soapenv=\"http://schemas.xmlsoap.org/soap/envelope/\" xmlns:urn=\"urn:ws-user-account\">\n<soapenv:Header/>\n<soapenv:Body>\n<urn:getAdminInfo soapenv:encodingStyle=\"http://schemas.xmlsoap.org/soap/encoding/\">\n</urn:getAdminInfo>\n</soapenv:Body>\n</soapenv:Envelope>
Sending the above request results in a 500 response!
\nScrolling down reveals that the only admin user could invoke this method:
\n
So it seems like there is some restriction on the invocation of this method.
\nStep 13: Bypass the SOAP body restrictions using the SOAPAction header.
\nThere is possibly a restriction on the invocation of the getAdminInfo method.
An alternative way to invoke a web service method is by using the SOAPAction header.
\nInformation:
\nThe SOAPAction header is a transport protocol header (either HTTP or JMS). It is transmitted with SOAP messages, and provides information about the intention of the web service request, to the service. The WSDL interface for a web service defines the SOAPAction header value used for each operation. Some web service implementations use the SOAPAction header to determine behavior.
Reference: https://www.ibm.com/docs/en/baw/19.x?topic=binding-protocol-headers
\nHead over to the WSDL file for the web service and inspect the soapaction attribute for the getAdminInfo operation:

SOAPAction attribute value:
\n
urn:ws-user-account#getAdminInfoNow head over to the Burp Repeater window and send the following request:
\nRequest:\n
POST /webservices/soap/ws-user-account.php HTTP/1.1\nAccept-Encoding: gzip,deflate\nContent-Type: text/xml;charset=UTF-8\nContent-Length: 228\nHost: localhost\nConnection: Keep-Alive\nUser-Agent: Apache-HttpClient/4.1.1 (java 1.5)\nSOAPAction: urn:ws-user-account#getAdminInfo\n<soapenv:Envelope xmlns:xsi=\"http://www.w3.org/2001/XMLSchema-instance\" xmlns:xsd=\"http://www.w3.org/2001/XMLSchema\" xmlns:soapenv=\"http://schemas.xmlsoap.org/soap/envelope/\" xmlns:urn=\"urn:ws-user-account\">\n</soapenv:Envelope>As you can notice, we are sending the SOAPAction header and have removed the SOAP request header and body.
\n
Sending the above request results in a 200 response!
\nScrolling down the response shows the details for the admin user and the second flag:
\n
flag2: 4315749f21a66fad53895daccbebf309
\nSo that was all about WSDL enumeration, invoking hidden methods, performing SQL injection and bypassing SOAP body restrictions.
\nStep 14: Open the DNS Lookup web service.
\nVisit Web Services > SOAP > Command Injection > DNS Lookup:
\n
That would take you to the following web page:
\n
Step 15: Check the WSDL file.
\nClick on the WSDL link to view the WSDL file for the provided web service:
\n
As you can see in the above image, lookupDNS is the only available operation:

Viewing the details for the lookupDNS operation:

The information on the web page reveals the input and output parameters expected by this operation. All this information could be inferred directly from the WSDL file as well.
\nScroll down to view the sample request:
\n
Step 16: Interact with the web service using Burp Suite.
\nCopy the sample request for the lookupDNS method to the Burp Repeater window:

Remove the /mutillidae part of the URL as the web service is located at /webservice and not at /mutillidae/webservice.
Once that is done, send the request:
\n
We got back a 200 response!
\nScroll down to view the DNS Lookup results:
\n
Step 17: Identifying command injection vulnerability.
\nSend a semicolon (;) instead of a hostname:

Scroll down to view the DNS Lookup results:
\n
Notice that the provided hostname was used as is and no errors were reported.
\nSend the following payload to the web service:
\nPayload:\n
;ls -alSending the above payload results in a 200 response:
\n
Scroll down to view the DNS Lookup results:
\n
Notice that the output for the ls -al command is retrieved!
So the web service is indeed vulnerable to command injection vulnerability.
\nStep 18: Retrieve the flag.
\nSince the DNS Lookup web service is vulnerable to a command injection vulnerability, send the following command to find the flag file:
\nPayload:\n
;find / -iname *flag* 2>/dev/nullSending the above payload results in a 200 response:
\n
The output reveals that the third flag is present in the file /app/flag3.
Send the following payload to read the flag file:
\nPayload:\n
;cat /app/flag3
flag3: 6ae5422a0f086335766e1de8f75c16b7
\nSo that was all about performing command injection attacks against web services.
\nAnd with that, we conclude this lab on attacking web services. There was a lot of ground to cover in this lab and we learned quite a lot of techniques to pentest SOAP-based web services and bypass SOAP body restrictions.
\n